Python in Cybersecurity: How to Build a Real-Time Network Intrusion Detection System
Introduction
In the ever-evolving landscape of technology, one of the most significant pieces of python news is the language’s meteoric rise in the field of cybersecurity. Once primarily the domain of C and Perl, security professionals and developers are increasingly turning to Python for its simplicity, readability, and an incredibly rich ecosystem of powerful libraries. This shift has democratized the development of security tools, enabling rapid prototyping and the creation of sophisticated systems for defense, forensics, and analysis. From automating security tasks to penetration testing, Python has become the Swiss Army knife for the modern security expert.
One of the most compelling applications of Python in this domain is the construction of Intrusion Detection Systems (IDS). An IDS is a critical component of network security, acting as a vigilant sentinel that monitors network traffic for malicious activity or policy violations. Traditionally, building such a system was a complex undertaking. However, with Python, developers can leverage high-level libraries to create a functional, real-time IDS from scratch. This article will provide a comprehensive, hands-on guide to building a basic but effective real-time network IDS using Python, exploring the core concepts, practical code, and best practices along the way.
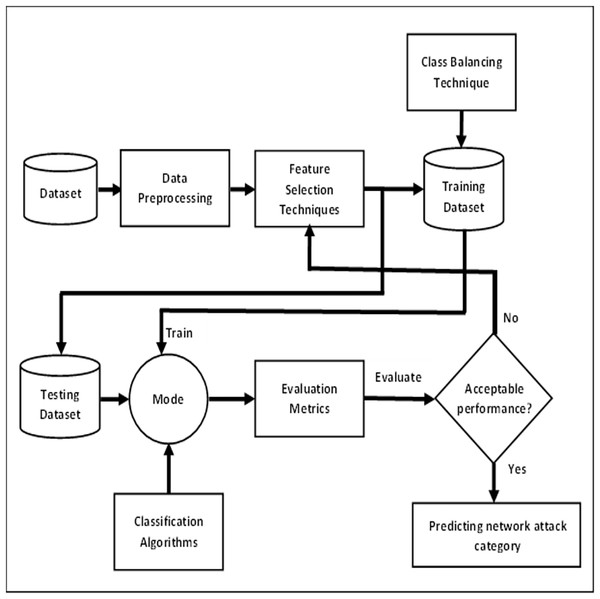
Section 1: The Architecture of a Python-Based Intrusion Detection System
Before diving into code, it’s crucial to understand the fundamental components and concepts that form the backbone of any network IDS. A well-designed system, even a basic one, is more than just a script; it’s an architecture designed to capture, analyze, and act upon network data in real-time. At its core, our Python-based IDS will consist of three primary stages: Packet Capture, Analysis Engine, and Alerting.
The Core Components
- Packet Capture (The Sniffer): This is the ears of our system. Its sole job is to listen to network traffic on a specific interface (e.g., your Wi-Fi or Ethernet card) and capture the raw data packets that flow through it. We will use the powerful Scapy library for this, which allows us to sniff network packets with just a few lines of Python.
- Analysis Engine (The Brains): Once a packet is captured, it’s passed to the analysis engine. This is where the logic resides. The engine dissects each packet, examining its headers and payload to determine if it matches a known threat signature or deviates from normal behavior. This is the most complex part of the IDS and can be implemented using two main methodologies.
- Alerting Mechanism (The Voice): If the analysis engine flags a packet or a series of packets as suspicious, the alerting mechanism is triggered. In a simple implementation, this could be printing a warning to the console. In a more advanced system, it could involve logging the event to a file, sending an email or Slack notification, or even integrating with a firewall to block the suspicious IP address.
Detection Methodologies: Signature vs. Anomaly
The effectiveness of an IDS hinges on its detection logic. There are two primary approaches:
1. Signature-Based Detection: This method works like a traditional antivirus program. It maintains a database of predefined rules or “signatures” of known malicious activities. For example, a signature could be a specific pattern in a packet’s payload that indicates a known malware, or a sequence of packets that matches a known attack like a port scan. This approach is highly effective at detecting known threats but is completely blind to new, zero-day attacks for which no signature exists.
2. Anomaly-Based Detection: This more advanced approach first establishes a baseline of “normal” network behavior. It learns what your network’s traffic patterns, protocols, and data volumes typically look like. The IDS then monitors the network for any deviations from this baseline. A sudden spike in traffic from a single IP, the use of an unusual port, or a connection to a blacklisted country could all be flagged as anomalies. This method can potentially detect novel attacks but is often more prone to “false positives” if the baseline isn’t well-defined.
For our practical example, we will start by implementing a simple signature-based engine and then explore the concepts behind a basic anomaly-based detector.
Section 2: Hands-On: Building the Packet Sniffer and Analyzer with Scapy
network intrusion detection dashboard – A few-shot network intrusion detection method based on mutual …
Now, let’s translate theory into practice. Our primary tool for this section will be Scapy, a powerful Python library that enables the user to send, sniff, dissect, and forge network packets. It’s an indispensable tool for network analysis and security research.
Setting Up Your Environment
First, you need to install Scapy. It’s recommended to do this within a Python virtual environment to avoid conflicts with system-wide packages.
pip install scapyNote: On Linux, you may need to run your Python script with `sudo` privileges to allow it to access raw network sockets for sniffing.
Capturing Network Traffic: The Sniffer
With Scapy, capturing live network traffic is remarkably straightforward. The `sniff()` function is the workhorse here. It listens on a network interface and calls a specified function for each packet it captures.
Let’s create a simple sniffer. This code will capture 10 packets and print a summary of each one.
from scapy.all import sniff
def packet_callback(packet):
"""
This function is called for each captured packet.
"""
print(packet.summary())
def main():
"""
Main function to start the sniffer.
"""
print("Starting packet sniffer...")
# Sniff 10 packets and then stop. For continuous sniffing, remove the 'count' parameter.
sniff(prn=packet_callback, count=10)
print("Sniffer stopped.")
if __name__ == "__main__":
main()
Dissecting Packets for Deeper Analysis
A simple summary isn’t enough for an IDS. We need to dig into the packet’s layers to extract meaningful information like IP addresses, ports, and protocols. Scapy represents packets as a series of layers (e.g., Ethernet, IP, TCP, UDP). We can check for the presence of a layer and access its fields using dictionary-like syntax.
Let’s enhance our `packet_callback` function to extract and display IP and TCP/UDP information.
from scapy.all import sniff, IP, TCP, UDP
class PacketAnalyzer:
def __init__(self):
pass
def process_packet(self, packet):
"""
Processes a single packet to extract relevant information.
"""
if packet.haslayer(IP):
ip_layer = packet.getlayer(IP)
src_ip = ip_layer.src
dst_ip = ip_layer.dst
protocol = ip_layer.proto
print(f"[+] New Packet: {src_ip} -> {dst_ip}")
if packet.haslayer(TCP):
tcp_layer = packet.getlayer(TCP)
src_port = tcp_layer.sport
dst_port = tcp_layer.dport
print(f" Protocol: TCP | Source Port: {src_port} -> Destination Port: {dst_port}")
elif packet.haslayer(UDP):
udp_layer = packet.getlayer(UDP)
src_port = udp_layer.sport
dst_port = udp_layer.dport
print(f" Protocol: UDP | Source Port: {src_port} -> Destination Port: {dst_port}")
def main():
analyzer = PacketAnalyzer()
print("Starting IDS packet analyzer...")
# Use 'iface' to specify your network interface, e.g., 'eth0' or 'en0'
# sniff(prn=analyzer.process_packet, store=False, iface='en0')
sniff(prn=analyzer.process_packet, store=False) # store=False for better memory management
if __name__ == "__main__":
main()
In this improved version, we’ve created a `PacketAnalyzer` class, which is a good practice for organizing our logic. The `process_packet` method checks for the IP layer and then for TCP or UDP layers within it, extracting the source/destination IPs and ports. This detailed information is the raw material for our detection engine.
Section 3: Implementing Detection Logic and Alerting
With our packet analyzer in place, we can now build the “brains” of our IDS. We’ll start with a simple signature-based rule to detect a common reconnaissance activity: a TCP port scan. Then, we’ll discuss a conceptual approach for anomaly detection.
network intrusion detection dashboard – Network intrusion detection using oversampling technique and …
Signature-Based Detection: Identifying a Port Scan
A simple port scan often involves one source IP trying to connect to many different ports on a single destination IP in a short period. We can detect this by tracking connection attempts. We’ll store recent connection attempts from source IPs and if a single IP exceeds a certain threshold of unique ports contacted, we’ll raise an alert.
Let’s add this logic to our `PacketAnalyzer` class.
from collections import defaultdict
from scapy.all import sniff, IP, TCP
import time
class IntrusionDetector:
def __init__(self, threshold=10, time_window=60):
# defaultdict(set) creates a set for any new key automatically
self.ip_port_scan_tracker = defaultdict(set)
self.ip_timestamps = {}
self.SCAN_THRESHOLD = threshold # Num of unique ports to trigger alert
self.TIME_WINDOW = time_window # Time in seconds
def detect_port_scan(self, packet):
if not packet.haslayer(TCP) or not packet.haslayer(IP):
return
src_ip = packet[IP].src
dst_port = packet[TCP].dport
current_time = time.time()
# Clean up old entries outside the time window
if src_ip in self.ip_timestamps and current_time - self.ip_timestamps[src_ip] > self.TIME_WINDOW:
# Reset the tracking for this IP
self.ip_port_scan_tracker[src_ip].clear()
self.ip_timestamps[src_ip] = current_time
# Add the new port to the set for this IP
self.ip_port_scan_tracker[src_ip].add(dst_port)
self.ip_timestamps.setdefault(src_ip, current_time)
# Check if the number of unique ports exceeds the threshold
if len(self.ip_port_scan_tracker[src_ip]) > self.SCAN_THRESHOLD:
self.alert(f"Potential Port Scan Detected from IP: {src_ip}")
# Reset after alerting to avoid continuous alerts for the same scan
self.ip_port_scan_tracker[src_ip].clear()
def alert(self, message):
# A simple alerting mechanism
print(f"[!] ALERT: {message}")
def process_packet(self, packet):
# We can add more detection methods here in the future
self.detect_port_scan(packet)
def main():
ids = IntrusionDetector(threshold=20, time_window=60)
print("Starting Intrusion Detection System...")
sniff(prn=ids.process_packet, store=False)
if __name__ == "__main__":
main()
In this code, we use a `defaultdict(set)` to efficiently store the unique destination ports contacted by each source IP. We also track timestamps to ensure our detection window is limited (e.g., 20 unique ports within 60 seconds). When the threshold is crossed, the `alert` method is called.
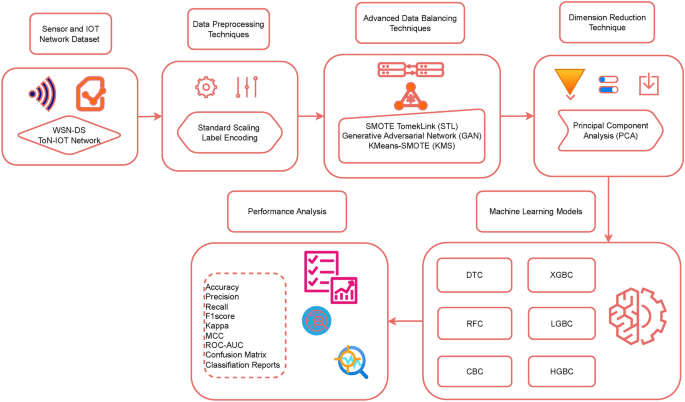
Conceptual Anomaly Detection: Monitoring Traffic Volume
A full-fledged anomaly detection system often requires machine learning. However, we can implement a simpler version based on statistical methods. The idea is to monitor a metric, like packets-per-second (PPS), establish a normal baseline, and then flag significant deviations.
Here’s a conceptual class structure for how you might approach this:
import time
class TrafficMonitor:
def __init__(self, alert_threshold_factor=2.0):
self.packet_count = 0
self.last_check_time = time.time()
self.pps_baseline = 100 # Packets per second, could be learned over time
self.pps_std_dev = 20 # Standard deviation, also learned
self.ALERT_THRESHOLD_FACTOR = alert_threshold_factor
def process_packet(self, packet):
self.packet_count += 1
current_time = time.time()
elapsed_time = current_time - self.last_check_time
# Check the volume every 5 seconds
if elapsed_time >= 5.0:
current_pps = self.packet_count / elapsed_time
print(f"Current traffic: {current_pps:.2f} PPS")
# Calculate the anomaly threshold
anomaly_threshold = self.pps_baseline + (self.pps_std_dev * self.ALERT_THRESHOLD_FACTOR)
if current_pps > anomaly_threshold:
self.alert(f"High traffic anomaly detected! PPS: {current_pps:.2f}")
# In a real system, you would continuously update the baseline
# self.update_baseline(current_pps)
# Reset counters
self.packet_count = 0
self.last_check_time = current_time
def alert(self, message):
print(f"[!] ANOMALY ALERT: {message}")
This example calculates the PPS every five seconds. If the current PPS exceeds a threshold defined by the baseline plus a multiple of the standard deviation, it triggers an alert. A real system would need a “learning mode” to dynamically calculate the `pps_baseline` and `pps_std_dev` over a period of normal network activity.
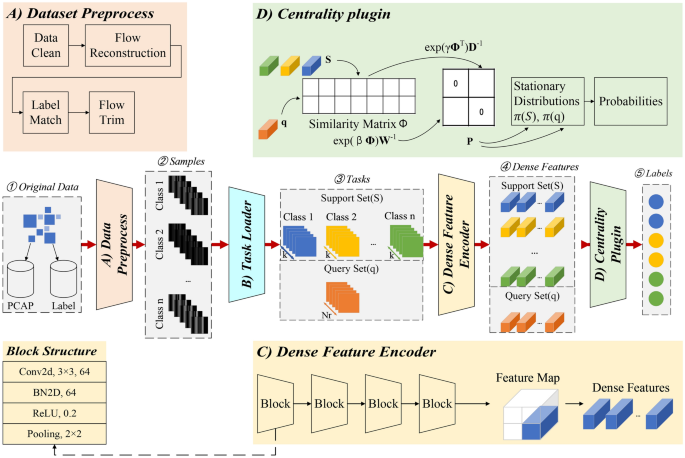
network intrusion detection dashboard – A hybrid machine learning model for intrusion detection in …
Section 4: Best Practices, Performance, and Real-World Considerations
Building a toy IDS is a fantastic learning experience, but deploying a similar system in a real-world environment requires additional considerations. Python is excellent for prototyping, but performance can become a bottleneck on high-traffic networks.
Performance Optimization
- The GIL Problem: Python’s Global Interpreter Lock (GIL) means that even on a multi-core processor, a standard Python process can only execute on one core at a time. For a high-throughput sniffer, this can be a major limitation.
- Packet Processing Overhead: The logic inside your packet processing function should be as fast as possible. Avoid slow operations like disk I/O or complex computations that could cause you to drop packets.
- Use C-based Libraries: For serious performance, consider offloading the packet capture to a more performant library written in C, like `pcapy` or `pylibpcap`, and use Python primarily for the analysis logic.
- Offload Analysis: A common architectural pattern is to have a lightweight Python sniffer that does minimal processing and simply forwards packets or extracted metadata to a separate analysis engine, possibly via a fast message queue like RabbitMQ or Kafka.
Common Pitfalls and How to Avoid Them
- False Positives: Your IDS is only as good as its rules. Poorly written rules can generate a flood of false alerts, leading to “alert fatigue” where real threats might be ignored. It’s critical to test and tune your rules against real network traffic. For anomaly detection, a proper learning phase is essential to establish an accurate baseline.
- False Negatives: This is the opposite problem—failing to detect a real threat. This can happen if an attacker uses an unknown technique (for signature-based systems) or if their malicious activity is subtle enough to fall within the “normal” baseline (for anomaly-based systems). A defense-in-depth strategy, where the IDS is just one of many security layers, is crucial.
- Legal and Ethical Considerations: Remember that sniffing network traffic can have serious privacy implications. Always ensure you have explicit permission to monitor any network. Unauthorized packet sniffing is illegal in many jurisdictions.
Conclusion
The latest python news continues to highlight the language’s versatility, and its application in cybersecurity is a testament to its power and flexibility. We’ve journeyed from the basic concepts of an Intrusion Detection System to building a functional prototype with Python and Scapy. We’ve seen how to capture and dissect packets, implement signature-based rules to detect threats like port scans, and conceptualized how to approach more advanced anomaly-based detection.
The key takeaway is that Python empowers developers and security professionals to rapidly build custom security tools tailored to their specific needs. While our example is a starting point, it demonstrates the core principles that underpin professional-grade security systems. By understanding these fundamentals and being mindful of real-world challenges like performance and rule-tuning, you can leverage Python to create powerful tools that help secure your network infrastructure. The world of cybersecurity is complex, but with Python, you have a formidable ally in your toolkit.