Django REST Framework Best Practices – Part 3
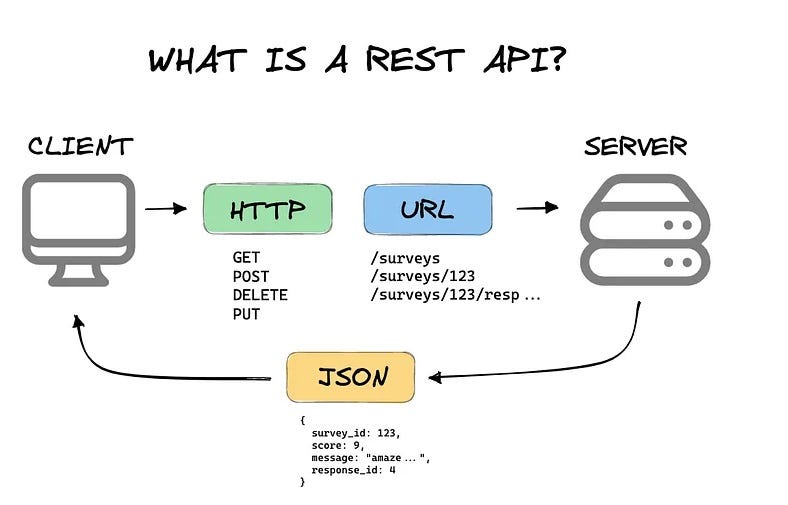
Welcome back to our comprehensive series on Django REST Framework (DRF). In Part 1 and Part 2, we laid the groundwork for building functional APIs. Now, it’s time to elevate your skills from building good APIs to building great ones. Master Django REST Framework with these essential best practices. Learn how to build scalable, maintainable REST APIs with proper serialization, authentication, and testing strategies. This is part 3 of our comprehensive series covering advanced techniques and practical implementations that separate production-ready applications from simple prototypes.
In the rapidly evolving world of web development, where the latest Python news often highlights new tools and frameworks, DRF remains a cornerstone for creating powerful and secure web services. As your applications grow in complexity, so do the challenges. How do you handle complex data relationships without killing your database? How do you enforce intricate, object-level permissions? And how do you ensure your API remains reliable and bug-free as you add new features? This article dives deep into these advanced topics, providing you with the patterns and code examples needed to build truly professional-grade APIs that are scalable, secure, and easy to maintain.
Mastering Advanced Serialization Techniques
Serialization is the heart of any DRF application, but basic model serializers only scratch the surface. As your data models become more interconnected, you need more sophisticated serialization strategies to manage relationships efficiently, customize output, and enforce complex business rules.
Tackling the N+1 Query Problem with Nested Serializers
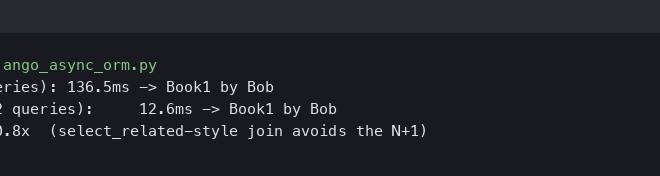
One of the most common performance bottlenecks in DRF is the “N+1 query” problem, which often arises when dealing with nested relationships. Imagine you have a Project model with a foreign key to multiple Task models. If you serialize a list of 10 projects and for each project, you serialize its tasks, you’ll end up with 1 query for the projects and 10 additional queries for the tasks (1 + N queries).
DRF’s nested serializers are powerful, but without proper query optimization, they can be performance killers. The solution lies in using Django’s queryset optimization tools: select_related (for one-to-one and foreign key relationships) and prefetch_related (for many-to-many and reverse foreign key relationships).
Consider these models:
# models.py
from django.db import models
from django.contrib.auth.models import User
class Project(models.Model):
owner = models.ForeignKey(User, related_name='projects', on_delete=models.CASCADE)
name = models.CharField(max_length=100)
created_at = models.DateTimeField(auto_now_add=True)
class Task(models.Model):
project = models.ForeignKey(Project, related_name='tasks', on_delete=models.CASCADE)
title = models.CharField(max_length=200)
completed = models.BooleanField(default=False)
To efficiently serialize a project with its tasks, you should override the get_queryset method in your ViewSet.
# views.py
from rest_framework import viewsets
from .models import Project
from .serializers import ProjectSerializer
from .permissions import IsOwnerOrReadOnly
class ProjectViewSet(viewsets.ModelViewSet):
serializer_class = ProjectSerializer
permission_classes = [IsOwnerOrReadOnly] # We'll define this later
def get_queryset(self):
"""
Optimize queryset to prevent N+1 queries.
"""
# Prefetch related tasks and select related owner in a single trip to the DB.
return Project.objects.prefetch_related('tasks').select_related('owner')
def perform_create(self, serializer):
serializer.save(owner=self.request.user)
By using prefetch_related('tasks'), you fetch all tasks for all projects in the main queryset with just one extra query, reducing the total queries from N+1 to just 2, regardless of the number of projects. This is a critical optimization for any read-heavy endpoint.
Dynamic Fields and Context-Aware Serialization
Sometimes, you need to serialize data differently based on the context, such as the user’s role or the specific request action (e.g., list vs. detail view). You can achieve this by accessing the context object within your serializer.
For example, let’s say you only want to show the full list of tasks in the detail view of a project, but just a count of tasks in the list view.
# serializers.py
from rest_framework import serializers
from .models import Project, Task
class TaskSerializer(serializers.ModelSerializer):
class Meta:
model = Task
fields = ['id', 'title', 'completed']
class ProjectSerializer(serializers.ModelSerializer):
# This field will be dynamically populated
tasks = serializers.SerializerMethodField()
task_count = serializers.IntegerField(source='tasks.count', read_only=True)
owner_username = serializers.CharField(source='owner.username', read_only=True)
class Meta:
model = Project
fields = ['id', 'name', 'owner_username', 'created_at', 'task_count', 'tasks']
def get_tasks(self, obj):
# Check the context for the view's action
view = self.context.get('view')
if view and view.action == 'retrieve':
# If it's a detail view, serialize all tasks
return TaskSerializer(obj.tasks.all(), many=True).data
# Otherwise (e.g., list view), return None or an empty list
return None
def to_representation(self, instance):
"""
Customize the output representation.
"""
representation = super().to_representation(instance)
# Remove the 'tasks' field if it's None (i.e., not a detail view)
if representation.get('tasks') is None:
representation.pop('tasks')
return representation
In this example, the get_tasks method checks the view’s action from the context. If it’s a detail view (retrieve), it serializes the tasks. Otherwise, it returns None, and the to_representation method removes the key from the final output, keeping your list view clean and lightweight.
Implementing Granular, Object-Level Permissions
DRF’s built-in permission classes like IsAuthenticated or IsAdminUser are great for endpoint-level security, but real-world applications often require more fine-grained, object-level control. For instance, a user should be able to edit their own project but not someone else’s.
Creating Custom Permission Classes
The key to object-level permissions is creating a custom permission class that inherits from permissions.BasePermission and implements the has_object_permission method. This method is called by DRF for detail views (GET, PUT, DELETE on /projects/{id}/) and receives the specific object being accessed.
Here’s how you can create a permission class that only allows the owner of an object to edit or delete it, while allowing any authenticated user to view it.
# permissions.py
from rest_framework import permissions
class IsOwnerOrReadOnly(permissions.BasePermission):
"""
Custom permission to only allow owners of an object to edit it.
Assumes the model instance has an `owner` attribute.
"""
def has_permission(self, request, view):
# Allow all authenticated users to access the endpoint (for list views)
return request.user and request.user.is_authenticated
def has_object_permission(self, request, view, obj):
# Read permissions are allowed to any request,
# so we'll always allow GET, HEAD or OPTIONS requests.
if request.method in permissions.SAFE_METHODS:
return True
# Write permissions are only allowed to the owner of the project.
return obj.owner == request.user
You then add this class to the permission_classes list in your ViewSet, as shown in the ProjectViewSet example earlier. Now, if a user tries to PUT or DELETE a project they don’t own, they will receive a 403 Forbidden response.
Bulletproof Your API with Comprehensive Testing
An untested API is a broken API waiting to happen. A robust test suite is non-negotiable for building maintainable and reliable applications. DRF provides excellent tools for testing, built on top of Django’s testing framework.
Setting Up Your Test Environment with APITestCase
DRF’s APITestCase class is your primary tool. It extends Django’s TestCase with helpful utilities for making API requests and asserting responses.
A best practice is to use a “factory” library like factory-boy to generate realistic test data instead of using static fixtures. Factories are more flexible and maintainable.
# factories.py
import factory
from django.contrib.auth.models import User
from .models import Project, Task
class UserFactory(factory.django.DjangoModelFactory):
class Meta:
model = User
username = factory.Faker('user_name')
email = factory.Faker('email')
class ProjectFactory(factory.django.DjangoModelFactory):
class Meta:
model = Project
name = factory.Faker('sentence', nb_words=4)
owner = factory.SubFactory(UserFactory)
class TaskFactory(factory.django.DjangoModelFactory):
class Meta:
model = Task
title = factory.Faker('sentence', nb_words=6)
project = factory.SubFactory(ProjectFactory)
Writing Meaningful Tests for Logic and Permissions
Your tests should cover not just the “happy path” but also edge cases, validation errors, and permission denials. Let’s write a test for our IsOwnerOrReadOnly permission.
# tests.py
from rest_framework.test import APITestCase
from rest_framework import status
from django.urls import reverse
from .factories import UserFactory, ProjectFactory
class ProjectAPITests(APITestCase):
def setUp(self):
self.user1 = UserFactory()
self.user2 = UserFactory()
self.project = ProjectFactory(owner=self.user1)
self.url = reverse('project-detail', kwargs={'pk': self.project.pk})
def test_owner_can_update_project(self):
"""
Ensure the owner of a project can update it.
"""
self.client.force_authenticate(user=self.user1)
data = {'name': 'Updated Project Name'}
response = self.client.put(self.url, data, format='json')
self.assertEqual(response.status_code, status.HTTP_200_OK)
self.project.refresh_from_db()
self.assertEqual(self.project.name, 'Updated Project Name')
def test_non_owner_cannot_update_project(self):
"""
Ensure a user who is not the owner cannot update the project.
"""
self.client.force_authenticate(user=self.user2)
data = {'name': 'Malicious Update'}
response = self.client.put(self.url, data, format='json')
self.assertEqual(response.status_code, status.HTTP_403_FORBIDDEN)
def test_unauthenticated_user_cannot_update_project(self):
"""
Ensure unauthenticated users cannot update any project.
"""
data = {'name': 'Anonymous Update'}
response = self.client.put(self.url, data, format='json')
self.assertEqual(response.status_code, status.HTTP_401_UNAUTHORIZED)
def test_any_authenticated_user_can_view_project(self):
"""
Ensure any authenticated user can view a project (read-only).
"""
self.client.force_authenticate(user=self.user2)
response = self.client.get(self.url)
self.assertEqual(response.status_code, status.HTTP_200_OK)
self.assertEqual(response.data['name'], self.project.name)
These tests explicitly verify the behavior of your custom permission class, giving you confidence that your security logic is working as intended. This level of testing is essential for any serious Python project and is a frequent topic in developer circles and tech news.
API Versioning and Final Recommendations
As your API evolves, you will inevitably need to make breaking changes. Without a versioning strategy, these changes can break client applications that depend on your API. DRF provides several versioning schemes, with URLPathVersioning being a popular and explicit choice.
Implementing API Versioning
With URLPathVersioning, the version is included in the URL, for example: /api/v1/projects/ and /api/v2/projects/. This makes it clear which version of the API the client is targeting.
To set it up:
- Add the versioning scheme to your DRF settings in
settings.py:REST_FRAMEWORK = { 'DEFAULT_VERSIONING_CLASS': 'rest_framework.versioning.URLPathVersioning', # ... other settings } - Update your
urls.pyto include the version parameter:# urls.py from django.urls import path, include urlpatterns = [ path('api/<str:version>/', include('yourapp.urls')), # ... other paths ]
Now you can create different serializers or views for different versions of your API, allowing you to gracefully introduce changes without breaking existing integrations. For example, you could check self.request.version in a view to return different data for ‘v1’ and ‘v2’.
Final Recommendations for Scalability
- Use Asynchronous Tasks: For long-running operations triggered by an API call (like sending an email or processing a large file), use a task queue like Celery. Respond to the user immediately with a
202 Acceptedstatus and perform the work in the background. - Implement Caching: For data that doesn’t change often, use a caching layer (like Redis) to store API responses. This can dramatically reduce database load and improve response times for high-traffic, read-only endpoints.
- Monitor and Log: Use tools like Sentry for error tracking and Prometheus/Grafana for performance monitoring. Understanding how your API behaves in production is key to identifying bottlenecks and improving reliability.
Conclusion
Moving beyond the basics of Django REST Framework is about embracing practices that lead to scalable, secure, and maintainable APIs. In this article, we’ve explored three critical areas: advanced serialization to optimize performance and customize output, granular object-level permissions to enforce complex security rules, and comprehensive testing to ensure reliability. By optimizing your database queries, implementing custom permissions, and writing a robust test suite, you are building a foundation for a professional-grade application that can grow and evolve. These techniques are not just “nice-to-haves”; they are essential for any serious project and represent the standard of quality expected in the modern development landscape.