Python in Cybersecurity: Building a Real-Time Network Intrusion Detection System
In today’s hyper-connected digital landscape, the need for robust cybersecurity has never been more critical. As network traffic grows exponentially, so do the opportunities for malicious actors to exploit vulnerabilities. Traditional security measures are often not enough to combat sophisticated, zero-day attacks. This is where Intrusion Detection Systems (IDS) play a pivotal role, acting as vigilant sentinels for our networks. The latest python news in the development community highlights a significant trend: leveraging Python’s power and simplicity to build custom, intelligent, and effective security tools. Its extensive ecosystem of libraries for networking, data analysis, and machine learning makes it the perfect language for this task.
This article provides a comprehensive technical guide on how to build a real-time network intrusion detection system using Python. We will explore the fundamental architecture, from capturing raw network packets to applying machine learning for intelligent anomaly detection. We’ll delve into practical code examples using industry-standard libraries like Scapy, Pandas, and Scikit-learn, offering actionable insights for developers, security analysts, and anyone interested in the practical application of Python in cybersecurity. By the end, you will understand the core principles and have a foundational blueprint for creating your own Python-powered IDS.
Why Python for Network Security?
Python’s ascent in the world of cybersecurity is no accident. It offers a unique combination of simplicity, power, and an unparalleled library ecosystem that makes it an ideal choice for developing security tools, including an IDS. Its suitability stems from several key advantages that streamline the development process from initial prototype to a functional system.
Simplicity and Speed of Development
Cybersecurity is a field of rapid response. Security analysts and developers need to create and deploy tools quickly to counter emerging threats. Python’s clean, readable syntax significantly reduces development time compared to lower-level languages like C++ or Java. This allows for rapid prototyping, testing, and iteration, enabling teams to build custom solutions tailored to their specific network environment without getting bogged down in complex boilerplate code.
A Rich Ecosystem of Specialized Libraries
Python’s true power lies in its vast collection of open-source libraries that provide pre-built functionality for almost any task imaginable. For building an IDS, a few libraries are indispensable:
Scapy: A powerful and versatile packet manipulation library. It allows you to sniff, forge, dissect, and send network packets. For an IDS, its primary role is capturing live network traffic for analysis.
Pandas & NumPy: These are the cornerstones of data analysis in Python. Pandas provides high-performance, easy-to-use data structures (like the DataFrame), while NumPy offers support for large, multi-dimensional arrays and matrices. Together, they are used to structure, clean, and prepare network data for analysis.
Scikit-learn: A comprehensive machine learning library that offers simple and efficient tools for data mining and data analysis. For an anomaly-based IDS, Scikit-learn provides a suite of unsupervised learning algorithms perfect for identifying unusual patterns in network traffic.
Matplotlib & Seaborn: While not part of the core IDS logic, these visualization libraries are crucial for understanding network data, analyzing model performance, and generating reports on detected threats.
Types of Intrusion Detection Systems
Using Python, we can effectively build the two primary types of IDS:
Signature-based IDS: This method works like an antivirus program. It maintains a database of known malicious patterns, or “signatures” (e.g., specific packet payloads, known malicious IP addresses, or unique traffic sequences associated with a known attack). It compares incoming traffic against this database and raises an alert if a match is found. While effective against known threats, it cannot detect novel, zero-day attacks.
Anomaly-based IDS: This more advanced approach uses machine learning to build a statistical model of what constitutes “normal” network behavior. It establishes a baseline and then monitors traffic for any deviations or anomalies that could indicate a new, unknown threat. This is where Python’s data science libraries truly shine, enabling the creation of intelligent systems that can adapt and learn.
Building a Practical IDS: From Packets to Insights
Keywords:
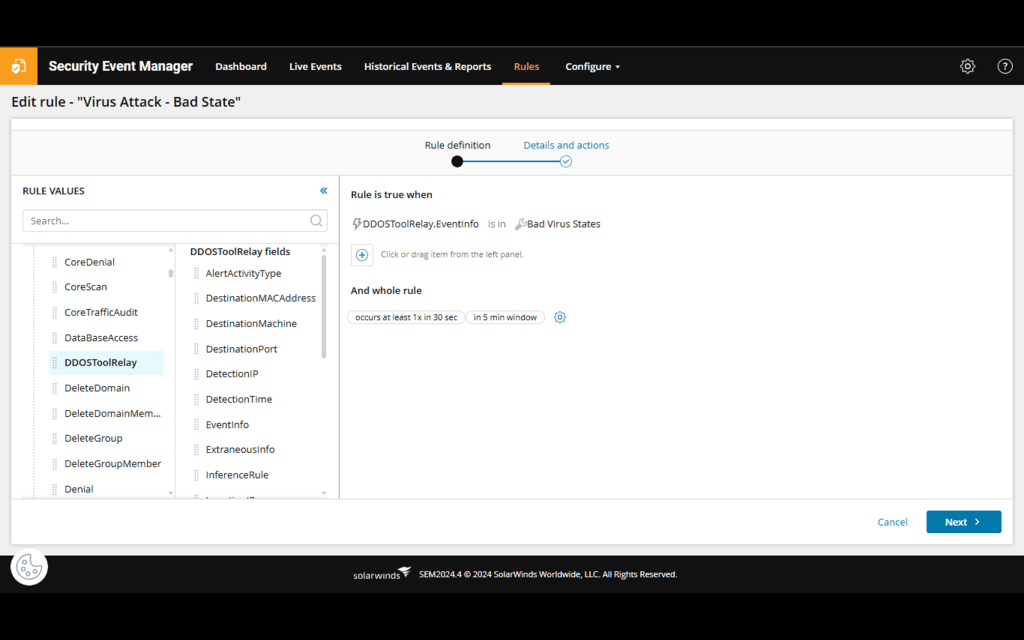
Cybersecurity dashboard – Top 10 Cybersecurity Dashboard Templates With Samples and …
Let’s break down the architecture of a Python-based IDS into three core steps: capturing network data, extracting meaningful features, and structuring that data for analysis. This process transforms a chaotic stream of raw packets into an organized dataset ready for inspection.
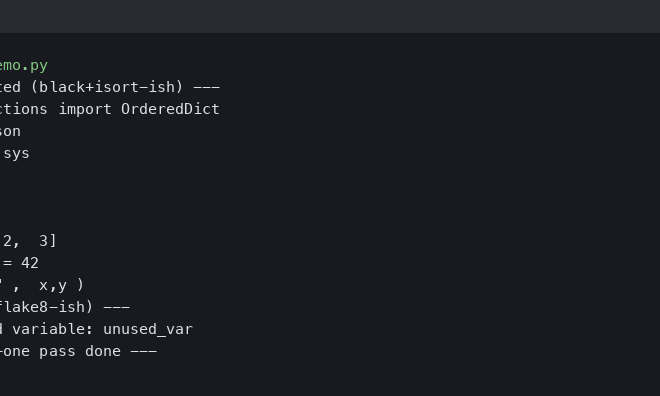
Step 1: Network Packet Capture with Scapy
The first step is to listen to the network traffic. The Scapy library makes this incredibly straightforward. Its sniff() function can capture packets from a specified network interface in real-time. We can provide a callback function that will be executed for every packet captured, allowing us to process them as they arrive.
Here is a basic Python script to start sniffing network traffic. This code sets up a sniffer on the primary network interface and calls the process_packet function for each packet it sees.
import scapy.all as scapy
def process_packet(packet):
“””
This function is called for each captured packet.
For now, it just prints a summary.
“””
print(packet.summary())
def start_sniffer(interface):
“””
Starts the packet sniffer on a given interface.
“””
print(f”[*] Starting sniffer on interface {interface}…”)
# The ‘prn’ argument specifies the callback function.
# ‘store=False’ tells Scapy not to keep packets in memory.
scapy.sniff(iface=interface, store=False, prn=process_packet)
if __name__ == “__main__”:
# Replace ‘eth0’ with your actual network interface (e.g., ‘en0’ on macOS, ‘Ethernet’ on Windows)
network_interface = “eth0”
start_sniffer(network_interface)
Step 2: Feature Extraction and Data Processing
Raw packets are complex and not suitable for direct analysis. We need to extract relevant features from each packet to create a structured representation. Key features for network analysis include IP addresses, ports, protocol, packet length, and TCP flags (e.g., SYN, ACK, FIN), which can indicate the state of a network connection.
Let’s create a class to handle this feature extraction. This class will take a Scapy packet and pull out the necessary information, returning it in a clean dictionary format.
from scapy.all import TCP, UDP, IP
class PacketProcessor:
def __init__(self):
self.feature_names = [
‘src_ip’, ‘dst_ip’, ‘src_port’, ‘dst_port’,
‘protocol’, ‘pkt_len’, ‘tcp_flags’
]
def extract_features(self, packet):
“””
Extracts relevant features from a packet and returns them as a dictionary.
“””
features = {}
if IP in packet:
features[‘src_ip’] = packet[IP].src
features[‘dst_ip’] = packet[IP].dst
features[‘pkt_len’] = len(packet)
if TCP in packet:
features[‘protocol’] = ‘TCP’
features[‘src_port’] = packet[TCP].sport
features[‘dst_port’] = packet[TCP].dport
# Extract TCP flags (e.g., ‘S’ for SYN, ‘A’ for ACK)
features[‘tcp_flags’] = “”.join(flag for flag in packet[TCP].flags)
elif UDP in packet:
features[‘protocol’] = ‘UDP’
features[‘src_port’] = packet[UDP].sport
features[‘dst_port’] = packet[UDP].dport
features[‘tcp_flags’] = ” # UDP has no flags
else:
features[‘protocol’] = ‘Other’
features[‘src_port’] = 0
features[‘dst_port’] = 0
features[‘tcp_flags’] = ”
return features
return None
Step 3: Storing and Analyzing with Pandas
Once we have a stream of feature dictionaries, we need a way to manage and analyze this data. This is where Pandas comes in. We can collect these features in real-time and append them to a Pandas DataFrame. A DataFrame provides a powerful, tabular structure for data manipulation and is the standard input format for most machine learning libraries, including Scikit-learn.
Here’s how we can integrate the `PacketProcessor` with our sniffer and store the data in a DataFrame.
import pandas as pd
import scapy.all as scapy
# Assume PacketProcessor class from above is defined here
class IntrusionDetector:
def __init__(self, interface):
self.interface = interface
self.processor = PacketProcessor()
self.packet_data = []
self.df = pd.DataFrame(columns=self.processor.feature_names)
def process_packet(self, packet):
features = self.processor.extract_features(packet)
if features:
self.packet_data.append(features)
# For real-time analysis, we would process this packet immediately.
# For demonstration, we’ll collect a batch.
if len(self.packet_data) % 50 == 0:
print(f”Collected {len(self.packet_data)} packets…”)
self.update_dataframe()
def update_dataframe(self):
# In a real system, this would be more efficient.
new_df = pd.DataFrame(self.packet_data)
self.df = pd.concat([self.df, new_df], ignore_index=True)
self.packet_data = [] # Clear the list
print(“DataFrame updated:”)
print(self.df.tail())
def start(self):
print(f”[*] Starting IDS on interface {self.interface}…”)
scapy.sniff(iface=self.interface, store=False, prn=self.process_packet)
if __name__ == “__main__”:
ids = IntrusionDetector(interface=”eth0″)
ids.start()
Leveraging Machine Learning for Advanced Threat Detection
With our data capture and processing pipeline in place, we can now implement the “intelligent” part of our IDS. Using machine learning for anomaly detection is a hot topic in python news and cybersecurity research, as it promises to detect novel attacks that signature-based systems would miss. The goal is to train a model on what “normal” traffic looks like and then use it to identify outliers.
Keywords:
Cybersecurity dashboard – A Complete Guide To Cybersecurity SEO: How To Rank And Land More …
Establishing a “Normal” Baseline
The foundation of any anomaly-based IDS is a high-quality dataset of benign network traffic. This dataset is used to train the machine learning model. It’s crucial that this training data is representative of your network’s typical activity and is free from any attack traffic, as any anomalies in the training set could be learned as “normal.” In a real-world scenario, you would capture traffic over an extended period of normal operation to build this baseline.
Choosing the Right Algorithm
Since we are looking for unexpected patterns without pre-labeled attack data, this is a perfect use case for unsupervised learning algorithms. Some excellent choices available in Scikit-learn include:
Isolation Forest: This algorithm is highly efficient and effective for anomaly detection. It works by randomly partitioning the data, making anomalies (which are “few and different”) easier to isolate.
Local Outlier Factor (LOF): This algorithm measures the local density deviation of a given data point with respect to its neighbors. It considers a sample as an outlier if its density is significantly lower than that of its neighbors.
One-Class SVM: This algorithm learns a boundary that encompasses the high-density regions of the training data. Any new data point that falls outside this boundary is considered an anomaly.
Practical Implementation with Scikit-learn
Let’s implement an anomaly detector using the Isolation Forest algorithm. We’ll create a class that can be trained on a DataFrame of normal traffic and then used to predict whether new, incoming packets are anomalous.
First, the data needs to be preprocessed. Machine learning models work with numbers, so we need to convert categorical features like IP addresses and protocols into a numerical format. For simplicity, we’ll use one-hot encoding.
Keywords:
Cybersecurity dashboard – cert #oswe #offsec #websec #appsec #bugbounty #pentesting …
import pandas as pd
from sklearn.ensemble import IsolationForest
from sklearn.preprocessing import OneHotEncoder
class AnomalyDetector:
def __init__(self, contamination=0.01):
# Contamination is the expected proportion of anomalies in the data set.
self.model = IsolationForest(contamination=contamination, random_state=42)
self.encoder = OneHotEncoder(handle_unknown=’ignore’)
self.is_trained = False
def preprocess_data(self, df, fit_encoder=False):
“””
Preprocesses the DataFrame for the model.
Converts categorical features to numerical using One-Hot Encoding.
“””
# Select categorical and numerical features
categorical_cols = df.select_dtypes(include=[‘object’, ‘category’]).columns
numerical_cols = df.select_dtypes(include=[‘number’]).columns
# Apply one-hot encoding
if fit_encoder:
self.encoder.fit(df[categorical_cols])
encoded_data = self.encoder.transform(df[categorical_cols])
# Combine numerical and encoded categorical data
processed_df = pd.concat(
[df[numerical_cols].reset_index(drop=True),
pd.DataFrame(encoded_data.toarray(), columns=self.encoder.get_feature_names_out(categorical_cols))],
axis=1
)
return processed_df
def train(self, df_normal_traffic):
“””
Trains the Isolation Forest model on a DataFrame of normal traffic.
“””
print(“[*] Training anomaly detection model…”)
processed_df = self.preprocess_data(df_normal_traffic, fit_encoder=True)
self.model.fit(processed_df)
self.is_trained = True
print(“[+] Model training complete.”)
def predict(self, df_new_traffic):
“””
Predicts if new traffic is an anomaly.
Returns a series where -1 is an anomaly and 1 is normal.
“””
if not self.is_trained:
raise RuntimeError(“Model has not been trained yet.”)
processed_df = self.preprocess_data(df_new_traffic)
predictions = self.model.predict(processed_df)
return predictions
# — Example Usage —
if __name__ == “__main__”:
# 1. Create dummy training data (in a real scenario, this is captured traffic)
normal_traffic = {
‘src_ip’: [‘192.168.1.10’] * 100, ‘dst_ip’: [‘8.8.8.8’] * 100,
‘src_port’: [50000] * 100, ‘dst_port’: [443] * 100,
‘protocol’: [‘TCP’] * 100, ‘pkt_len’: [60] * 100, ‘tcp_flags’: [‘A’] * 100
}
df_train = pd.DataFrame(normal_traffic)
# 2. Train the model
detector = AnomalyDetector()
detector.train(df_train)
# 3. Create new traffic data, including a potential anomaly
new_traffic = {
‘src_ip’: [‘192.168.1.10’, ‘10.0.0.5’],
‘dst_ip’: [‘8.8.8.8’, ‘192.168.1.10’],
‘src_port’: [50001, 12345],
‘dst_port’: [443, 6666],
‘protocol’: [‘TCP’, ‘UDP’],
‘pkt_len’: [60, 1500], # Large packet size is anomalous
‘tcp_flags’: [‘A’, ”]
}
df_test = pd.DataFrame(new_traffic)
# 4. Make predictions
results = detector.predict(df_test)
anomalies = df_test[results == -1]
print(“\n[!] Anomaly Detected:”)
print(anomalies)
Deploying Your Python IDS: Tips and Considerations
Building a prototype is one thing; deploying a robust and reliable IDS in a production environment is another. There are several practical considerations and common pitfalls to be aware of to ensure your system is effective and manageable.
Common Pitfalls to Avoid
High False Positive Rate: Anomaly-based systems are notoriously prone to false positives, where legitimate but unusual traffic is flagged as malicious. This can lead to “alert fatigue” for security teams. It’s crucial to carefully tune the model’s sensitivity (like the contamination parameter in Isolation Forest) and potentially add a whitelist for known-good but unusual behavior.
Performance Bottlenecks: High-traffic networks can generate millions of packets per second. Python, being an interpreted language, can struggle to keep up. The packet processing pipeline is the most likely bottleneck. For production systems, consider using more performant libraries, optimizing critical code paths with Cython, or offloading the packet capture to more specialized tools.
Encrypted Traffic: A significant portion of today’s internet traffic is encrypted with TLS/SSL. This means you cannot inspect the packet payload for malicious content. Your IDS will be limited to analyzing metadata (IPs, ports, packet sizes, traffic volume, and timing), which is still valuable but less comprehensive.
Best Practices for a Robust System
Continuous Learning and Retraining: Network behavior changes over time. A model trained on last year’s traffic may not be effective today. Implement a strategy for periodically retraining your model on fresh data to prevent “model drift” and ensure it remains accurate.
Adopt a Hybrid Approach: The most effective systems often combine signature-based and anomaly-based detection. Augment your ML model with a simple but fast signature-based engine that checks against blocklists of known malicious IPs or domains. This can catch common threats quickly, leaving the ML model to focus on novel attacks.
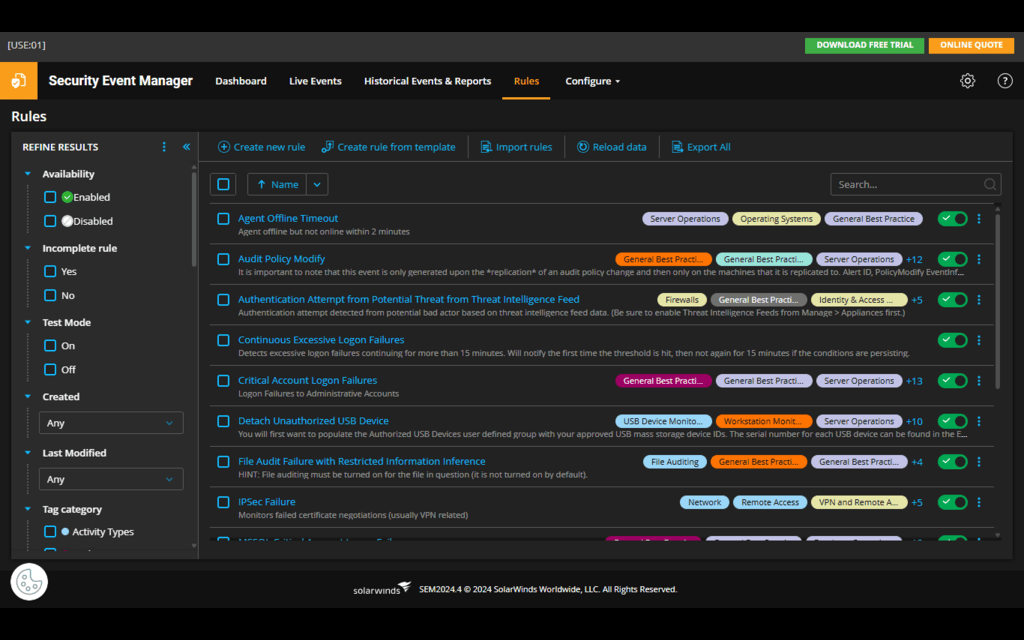
Robust Logging and Alerting: When an anomaly is detected, the system should generate a detailed log entry including all relevant packet features. This is crucial for forensic analysis. Alerts should be clear, actionable, and sent through appropriate channels (e.g., a SIEM, a Slack channel, or email) to ensure a timely response.
Final Thoughts: The Future of Python in Cybersecurity
We have journeyed from the basic concept of an IDS to building a functional, machine learning-powered prototype in Python. This exploration demonstrates Python’s profound capability as a first-class language for cybersecurity. By harnessing the power of libraries like Scapy for network interaction, Pandas for data manipulation, and Scikit-learn for intelligent analysis, we can construct sophisticated security tools that were once the exclusive domain of specialized vendors.
The example built here serves as a powerful proof of concept, illustrating the core principles of modern intrusion detection. As threats evolve, the ability to rapidly develop and deploy custom, intelligent, and adaptive security solutions will become increasingly vital. The ongoing developments in AI/ML libraries, a constant source of exciting python news, will only further solidify Python’s role in automating and enhancing the next generation of cybersecurity defenses. For developers and security professionals, mastering these tools is no longer just an advantage—it is a necessity.