Harnessing Python for Network Security: A Guide to Building a Real-Time Intrusion Detection System
Introduction
In an era of escalating digital threats, robust cybersecurity is no longer a luxury but a necessity. The ability to monitor network traffic in real-time to detect and respond to malicious activity is a cornerstone of modern defense strategies. While commercial solutions abound, the power and flexibility of open-source tools offer an unparalleled opportunity for customization and learning. Among these, Python has emerged as a dominant force in the cybersecurity landscape. Its simple syntax, vast ecosystem of powerful libraries, and rapid development capabilities make it the perfect language for building sophisticated security tools from the ground up. This convergence of Python and cybersecurity is a frequent topic in developer circles and python news, highlighting a growing trend of using high-level languages for low-level security tasks.
This article provides a comprehensive, technical guide to building a real-time Intrusion Detection System (IDS) using Python. We will explore the fundamental concepts of intrusion detection, walk through the core components of a Python-based IDS, and provide practical code examples for capturing, analyzing, and acting on network data. Whether you are a security professional looking to automate tasks, a developer curious about network programming, or a student eager to apply your Python skills to a real-world problem, this guide will equip you with the knowledge to build your own network monitoring solution.
The Foundations of Intrusion Detection with Python
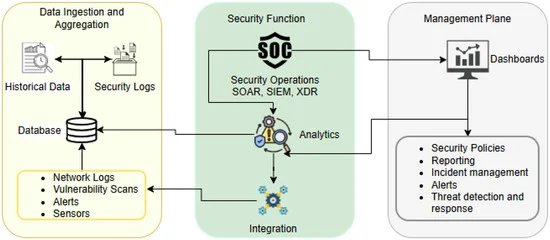
Before diving into code, it’s crucial to understand the “what” and “why” behind building an IDS. An Intrusion Detection System is a device or software application that monitors a network or systems for malicious activity or policy violations. Any detected activity is typically reported either to an administrator or collected centrally using a security information and event management (SIEM) system. The goal is to identify threats before they can cause significant damage.
Types of IDS: NIDS vs. HIDS
Intrusion Detection Systems are broadly categorized into two types, each serving a distinct purpose:
Network-based Intrusion Detection System (NIDS): A NIDS is placed at a strategic point within the network to monitor traffic to and from all devices on the network. It analyzes passing traffic by performing packet inspection and matching the traffic to a library of known attacks. The primary advantage is that it can monitor a large network with a single, well-placed sensor. For this article, our focus will be on building a simplified NIDS.
Host-based Intrusion Detection System (HIDS): A HIDS runs on an individual host or device on the network. It monitors the inbound and outbound packets from the device only and will alert the user or administrator if suspicious activity is detected. It can also monitor system files and logs for unauthorized changes, providing a granular view of a single machine’s security posture.
Why Python is the Ideal Choice for IDS Development
Python’s rise in the cybersecurity domain isn’t accidental. It offers a unique combination of features that make it exceptionally well-suited for building security tools like an IDS.
Rapid Prototyping: Python’s concise and readable syntax allows security engineers to quickly script, test, and deploy new detection rules and analysis logic. This agility is critical in a field where new threats emerge daily.
Rich Ecosystem of Libraries: Python’s strength is magnified by its extensive collection of third-party libraries. For network security, libraries like Scapy for packet manipulation, Pandas for data analysis, and Scikit-learn for machine learning provide powerful, pre-built functionalities that drastically reduce development time.
Readability and Maintainability: Security logic can become incredibly complex. Python’s emphasis on clean, readable code makes it easier for teams to collaborate on, maintain, and update the IDS over time.
Cross-Platform Compatibility: Python code can run on Windows, macOS, and Linux with minimal to no modification, making it possible to deploy a custom IDS across a heterogeneous network environment.
Building Blocks: Capturing and Analyzing Network Traffic
A functional IDS is built upon three core pillars: capturing network data, parsing it into a usable format, and analyzing it for signs of intrusion. Python, with its powerful libraries, excels at each of these stages.
Step 1: Packet Sniffing with Scapy
Keywords:
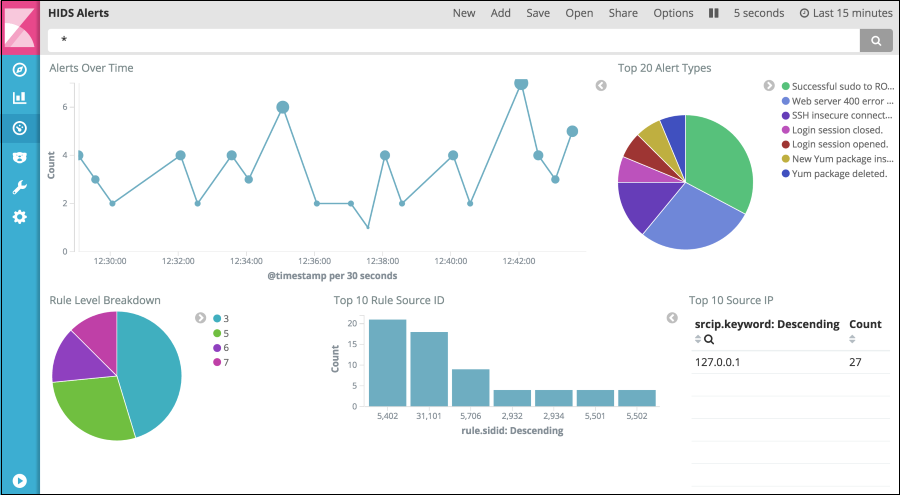
intrusion detection system dashboard – How to Monitor Host-Based Intrusion Detection System Alerts on …
The first step is to capture the raw data flowing through your network interface. For this, the Scapy library is the undisputed champion in the Python world. Scapy is a powerful interactive packet manipulation program and library that can forge or decode packets of a wide number of protocols, send them on the wire, capture them, and more. Here’s how to build a basic packet sniffer.
First, ensure you have Scapy installed:
pip install scapy
Next, you can write a simple script to start sniffing packets.
from scapy.all import sniff, IP, TCP
def packet_callback(packet):
“””
This function will be called for each captured packet.
“””
if packet.haslayer(IP):
ip_layer = packet.getlayer(IP)
src_ip = ip_layer.src
dst_ip = ip_layer.dst
print(f”[+] New Packet: {src_ip} -> {dst_ip}”)
def start_sniffer():
“””
Starts the packet sniffer.
“””
print(“[*] Starting packet sniffer…”)
# The ‘prn’ argument specifies the callback function to be executed for each packet
# The ‘store’ argument is set to 0 to prevent Scapy from storing packets in memory
sniff(prn=packet_callback, store=0)
if __name__ == “__main__”:
start_sniffer()
In this code, the `sniff` function from Scapy does the heavy lifting. We pass our `packet_callback` function to it, which Scapy then executes for every packet it captures. Setting `store=0` is a crucial performance optimization, as it tells Scapy not to keep a copy of every packet in memory, which would quickly become unsustainable on a busy network.
Step 2: Parsing Packet Data for Deeper Insights
Simply knowing the source and destination IP isn’t enough for an effective IDS. We need to dig deeper into the packet’s layers to extract more meaningful information, such as protocols, ports, and flags.
from scapy.all import sniff, IP, TCP, UDP
def detailed_packet_parser(packet):
“””
Parses and prints detailed information from a packet.
“””
if not packet.haslayer(IP):
return
ip_layer = packet.getlayer(IP)
src_ip = ip_layer.src
dst_ip = ip_layer.dst
protocol = ip_layer.proto
protocol_name = “”
src_port = None
dst_port = None
if protocol == 6 and packet.haslayer(TCP): # 6 is the protocol number for TCP
tcp_layer = packet.getlayer(TCP)
protocol_name = “TCP”
src_port = tcp_layer.sport
dst_port = tcp_layer.dport
elif protocol == 17 and packet.haslayer(UDP): # 17 is for UDP
udp_layer = packet.getlayer(UDP)
protocol_name = “UDP”
src_port = udp_layer.sport
dst_port = udp_layer.dport
if protocol_name:
print(f”[{protocol_name}] {src_ip}:{src_port} -> {dst_ip}:{dst_port}”)
# To use this, change the callback in the sniff function:
# sniff(prn=detailed_packet_parser, store=0)
This enhanced parser checks for TCP and UDP layers within the IP packet. By inspecting `ip_layer.proto`, we can determine the transport layer protocol and then access its specific attributes like source port (`sport`) and destination port (`dport`). This level of detail is essential for creating meaningful detection rules.
From Data to Detection: Implementing Analysis Logic
With a steady stream of parsed packet data, the next step is to build the “detection engine.” This engine will use a set of rules or models to decide if a given packet or sequence of packets is malicious. There are two primary approaches: signature-based and anomaly-based detection.
Signature-Based Detection: The Rulebook Approach
This is the most common method used in traditional IDS. It involves creating a database of “signatures”—patterns that correspond to known attacks. The IDS compares network traffic against these signatures and raises an alert if a match is found. A classic example is detecting a port scan, where an attacker rapidly probes multiple ports on a target machine to find open services.
Let’s implement a simple detector for a SYN port scan.
import time
from collections import defaultdict
# A simple in-memory store for tracking connection attempts
# In a real application, this might be a Redis cache or a database
connection_tracker = defaultdict(lambda: defaultdict(set))
SCAN_THRESHOLD = 10 # Number of different ports scanned to trigger an alert
TIME_WINDOW = 60 # Time window in seconds
def port_scan_detector(packet):
“””
A simple signature-based detector for TCP SYN port scans.
“””
if not (packet.haslayer(IP) and packet.haslayer(TCP)):
return
ip_layer = packet.getlayer(IP)
tcp_layer = packet.getlayer(TCP)
src_ip = ip_layer.src
dst_port = tcp_layer.dport
# We only care about SYN packets (the start of a connection)
# TCP flags: S=SYN, A=ACK, F=FIN, R=RST, P=PSH, U=URG
if tcp_layer.flags == ‘S’:
current_time = time.time()
# Add the destination port to the set of ports scanned by this source IP
connection_tracker[src_ip][‘ports’].add(dst_port)
# Set or update the timestamp for this IP
if ‘timestamp’ not in connection_tracker[src_ip]:
connection_tracker[src_ip][‘timestamp’] = current_time
# Check if the time window has expired
if current_time – connection_tracker[src_ip][‘timestamp’] > TIME_WINDOW:
# Reset for this IP if window expired
connection_tracker[src_ip][‘ports’] = {dst_port}
connection_tracker[src_ip][‘timestamp’] = current_time
# Check if the number of scanned ports exceeds our threshold
if len(connection_tracker[src_ip][‘ports’]) > SCAN_THRESHOLD:
print(f”[!] ALERT: Port scan detected from {src_ip}!”)
# Reset after alerting to avoid spamming alerts
del connection_tracker[src_ip]
# Use this as the callback: sniff(prn=port_scan_detector, store=0)
This function maintains a dictionary to track which source IPs are attempting to connect to which ports. If an IP attempts to connect to more than `SCAN_THRESHOLD` unique ports within the `TIME_WINDOW`, it triggers an alert. This is a basic but effective signature for a common reconnaissance technique.
Keywords:
intrusion detection system dashboard – How to Monitor Host-Based Intrusion Detection System Alerts on …
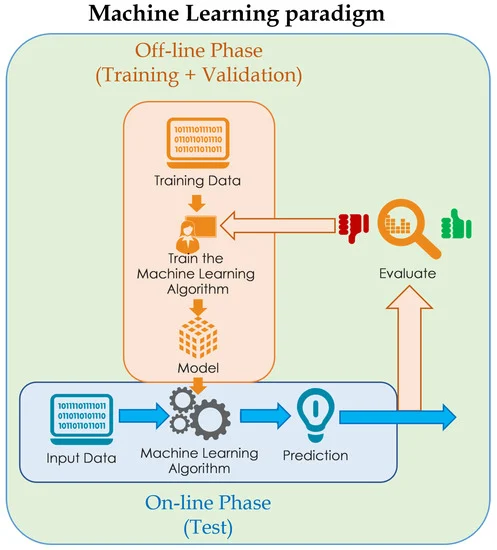
Anomaly-Based Detection: Learning Normal Behavior
A more advanced approach is anomaly detection, which often employs machine learning. Instead of looking for known bad patterns, this method establishes a baseline of what “normal” network traffic looks like. Any significant deviation from this baseline is flagged as a potential threat. This allows the IDS to potentially detect novel, zero-day attacks for which no signature exists.
Implementing a full-fledged ML-based IDS is complex, but we can outline the process and show a conceptual code snippet using Scikit-learn.
Data Collection & Feature Engineering: Collect a large dataset of normal network traffic. From this data, extract meaningful features like packet size, protocol ratios, connection duration, data transfer volume, etc.
Model Training: Use an unsupervised learning algorithm, like an Isolation Forest or a One-Class SVM, to train a model on the “normal” data. These models learn to identify outliers.
Real-Time Prediction: In your packet processing callback, extract the same features from live packets and feed them to the trained model. If the model classifies the new data point as an anomaly, raise an alert.
# Conceptual Example – Not a complete, runnable script
import pandas as pd
from sklearn.ensemble import IsolationForest
# — OFFLINE TRAINING PHASE —
# 1. Assume ‘normal_traffic.csv’ contains features from a baseline capture
# Features might include: packet_length, protocol_type, port_entropy, etc.
# df = pd.read_csv(‘normal_traffic.csv’)
# features = [‘packet_length’, ‘protocol_type’]
# X_train = df[features]
# 2. Train the model
# model = IsolationForest(contamination=0.01) # Assume 1% of data could be anomalies
# model.fit(X_train)
# — REAL-TIME DETECTION PHASE —
# In a real application, you would load the pre-trained model
# from joblib import load
# trained_model = load(‘ids_model.joblib’)
def anomaly_detector(packet_features):
“””
Uses a pre-trained model to detect anomalies.
`packet_features` would be a dictionary or list of features extracted from a live packet.
“””
# Create a DataFrame from the live features
# live_df = pd.DataFrame([packet_features])
# prediction = trained_model.predict(live_df) # -1 for anomaly, 1 for normal
# if prediction[0] == -1:
# print(f”[!] ALERT: Anomaly detected! Features: {packet_features}”)
pass # Placeholder for the real logic
This conceptual code illustrates the workflow. The real challenge lies in robust feature engineering and continuous model retraining to adapt to evolving network behavior. This area of security is a hot topic in python news and research, with new techniques constantly being developed.
From Prototype to Production: Practical Considerations
Building a proof-of-concept IDS is one thing; deploying a reliable, production-ready system is another. Several critical factors must be considered to bridge this gap.
Performance and Scalability
Packet sniffing and analysis are I/O and CPU-intensive operations. On a high-traffic network, a single-threaded Python script can quickly become a bottleneck. Python’s Global Interpreter Lock (GIL) can limit the effectiveness of multithreading for CPU-bound tasks. To scale, consider a multiprocessing architecture where one process captures packets and places them on a queue, while a pool of worker processes consumes from the queue to perform the analysis in parallel.
Python code cybersecurity – Funny Python Code Cybersecurity Poster by Me – Fine Art America
Common Pitfalls to Avoid
False Positives and Negatives: This is the eternal struggle of any IDS. A system that is too sensitive will flood administrators with false alerts (false positives), leading to alert fatigue. A system that is not sensitive enough will miss real threats (false negatives). Constant tuning of rules and models is required.
Encrypted Traffic: A significant portion of modern web traffic is encrypted with TLS/SSL. A NIDS cannot inspect the payload of encrypted packets without performing complex and often intrusive man-in-the-middle decryption, which has its own security and privacy implications.
Evasion Techniques: Sophisticated attackers know how IDS systems work and will employ techniques to evade detection, such as fragmenting packets, using polymorphic code, or tunneling traffic through legitimate protocols.
Integration and Alerting
An IDS is useless if its alerts go unnoticed. A robust alerting mechanism is essential. This can range from simple logging to more advanced integrations.
import logging
# Configure basic logging
logging.basicConfig(filename=’ids_alerts.log’, level=logging.WARNING,
format=’%(asctime)s – %(message)s’)
def log_alert(message):
“””
Logs a security alert to a file.
“””
logging.warning(message)
# Example usage within a detector
# if port_scan_detected:
# alert_message = f”Port scan detected from {src_ip}”
# log_alert(alert_message)
For more immediate notification, you could use Python libraries like `requests` to send alerts to a Slack channel via webhooks or `smtplib` to send an email to the security team.
Conclusion
Python has firmly established itself as a first-class citizen in the world of cybersecurity. Its combination of power, simplicity, and an extensive library ecosystem makes it an outstanding choice for building custom security tools like a real-time Intrusion Detection System. Throughout this article, we’ve journeyed from the fundamental concepts of network monitoring to the practical implementation of packet sniffing with Scapy, data analysis, and rule-based detection logic. We’ve also touched upon the more advanced realm of anomaly detection with machine learning and discussed the critical considerations for deploying a robust system.
Building an IDS is a challenging yet incredibly rewarding project that offers deep insights into networking, security protocols, and data analysis. While the examples provided here form a solid foundation, a production-grade system requires continuous refinement, performance optimization, and a deep understanding of the threat landscape. As cybersecurity challenges evolve, Python’s role will only continue to grow, making it an essential skill for the modern security professional and a constant source of innovation in the python news cycle.