Python Security Best Practices
Python’s simplicity, versatility, and vast ecosystem of libraries have made it one of the world’s most popular programming languages, powering everything from web applications and data science pipelines to machine learning models and IoT devices. However, this widespread adoption also makes Python applications a prime target for malicious actors. Securing your Python code is no longer an afterthought—it’s a critical, ongoing process essential for protecting data, maintaining user trust, and ensuring application integrity. A robust security posture involves more than just writing functional code; it requires a defensive mindset and a deep understanding of potential threats.
This comprehensive guide delves into the essential security best practices for Python developers. We will move beyond the basics to provide actionable advice, practical code examples, and strategic insights. You’ll learn how to fortify your applications by mastering input validation, implementing secure authentication and encryption, managing dependencies effectively, and preventing the most common vulnerabilities that plague modern software. By embracing these principles, you can transform your applications from potential liabilities into secure, resilient, and trustworthy systems. Staying informed on the latest security-related python news is also a key part of a developer’s responsibility in this evolving landscape.
Foundational Security Principles: Building a Secure Mindset
Before diving into specific vulnerabilities and tools, it’s crucial to adopt a security-first mindset. This means integrating security considerations into every stage of the development lifecycle, from initial design to deployment and maintenance. Three foundational principles form the bedrock of this approach: the Principle of Least Privilege, rigorous input validation, and Defense in Depth.
The Principle of Least Privilege
The Principle of Least Privilege (PoLP) dictates that any user, program, or process should only have the minimum permissions necessary to perform its function. By limiting access rights, you significantly reduce the potential damage if a component is compromised. An attacker who gains control of a process with limited privileges will have a much harder time escalating their access to compromise the entire system.
In a Python context, this means:
- Filesystem Access: If your application only needs to read from a specific directory, its user account should not have write or execute permissions for that directory, nor any access to other parts of the filesystem.
- Database Permissions: Create dedicated database users for your application with granular permissions. A user for a web application that primarily reads data should not have `DROP TABLE` or administrative privileges. Grant only `SELECT`, `INSERT`, `UPDATE`, and `DELETE` rights on specific tables as needed.
- Running Processes: Never run your Python application (e.g., a Django or Flask server) as the `root` user. Create a dedicated, unprivileged user account for the application. If an attacker finds a remote code execution vulnerability, their impact will be confined to what that unprivileged user can do.
Input Validation and Sanitization: The First Line of Defense
Never trust data that comes from an external source. This is the golden rule of application security. Any data originating from users, APIs, or other services can be crafted to exploit vulnerabilities. Input validation and sanitization are your primary tools for mitigating this risk.
- Validation: This is the process of ensuring that input data conforms to the expected format, type, and range. For example, a user ID should be an integer, an email address must match a specific pattern, and a birth date must be a valid date in the past. Libraries like Pydantic are excellent for defining strict data models and automatically validating incoming data in APIs.
- Sanitization: This is the process of cleaning or filtering input to remove potentially malicious characters or code. A classic example is sanitizing user-submitted HTML to prevent Cross-Site Scripting (XSS) attacks. The bleach library is a powerful tool for this, allowing you to specify exactly which HTML tags and attributes are permissible.
Defense in Depth
No single security control is infallible. The Defense in Depth strategy involves creating multiple, overlapping layers of security. If one layer fails, another is in place to thwart the attack. For a Python web application, this layered approach might include a Web Application Firewall (WAF) at the edge, strict input validation in the application logic, a securely configured database with limited permissions, and robust logging and monitoring to detect suspicious activity. Each layer provides a distinct safeguard, making a successful breach significantly more difficult to achieve.
Tackling Common Vulnerabilities in Python Applications
Understanding common attack vectors is key to writing secure code. Many vulnerabilities stem from a few common mistakes that can be systematically avoided. Let’s explore some of the most critical threats and how to mitigate them in Python.
Injection Attacks (SQL, Command)
Injection attacks occur when untrusted input is passed directly to an interpreter as part of a command or query. This can trick the interpreter into executing unintended commands or accessing data without proper authorization.
SQL Injection: This is one of the most dangerous web vulnerabilities. It happens when an attacker can manipulate a SQL query by inserting their own SQL code into a user input field.

Vulnerable Example (DO NOT USE):
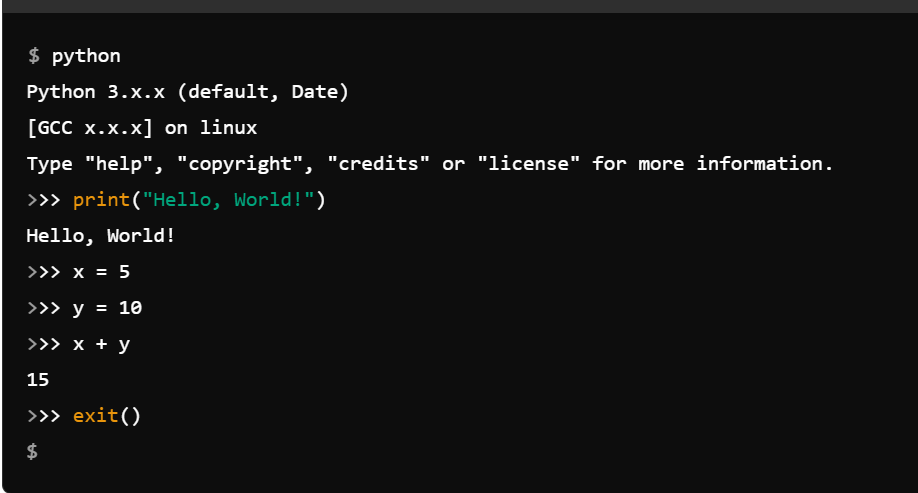
import sqlite3
# Assume user_input is from a web form, e.g., "' OR 1=1 --"
user_input = input("Enter username: ")
db = sqlite3.connect("example.db")
cursor = db.cursor()
# This is highly vulnerable!
query = f"SELECT * FROM users WHERE username = '{user_input}'"
cursor.execute(query) # The malicious input alters the query
Secure Solution (Parameterized Queries): Always use parameterized queries (also known as prepared statements). The database driver handles the safe substitution of values, treating the input strictly as data, not as executable code. ORMs like SQLAlchemy and Django’s ORM do this automatically.
import sqlite3
user_input = input("Enter username: ")
db = sqlite3.connect("example.db")
cursor = db.cursor()
# Secure way using a placeholder (?)
query = "SELECT * FROM users WHERE username = ?"
cursor.execute(query, (user_input,)) # The driver safely handles the input
Command Injection: This occurs when an application passes unsafe user input to a system shell. The `os.system()` and `subprocess` modules can be vectors if used improperly.
Vulnerable Example:
import os
# filename could be "my_file.txt; rm -rf /"
filename = input("Enter filename to list details: ")
os.system(f"ls -l {filename}") # Very dangerous!
Secure Solution: Avoid the shell when possible by passing arguments as a list. If you must use a shell command with user input, use `shlex.quote()` to escape shell metacharacters.
import subprocess
import shlex
filename = input("Enter filename to list details: ")
# Secure way: pass arguments as a list
subprocess.run(["ls", "-l", filename])
# Alternative secure way if a shell is needed
safe_filename = shlex.quote(filename)
subprocess.run(f"ls -l {safe_filename}", shell=True)
Cross-Site Scripting (XSS)
XSS vulnerabilities allow attackers to inject malicious scripts (usually JavaScript) into web pages viewed by other users. This can be used to steal session cookies, deface websites, or redirect users to malicious sites. Fortunately, modern Python web frameworks like Django and Flask (with Jinja2) provide strong default protections by auto-escaping all variable content rendered in templates. This converts characters like < and > into their HTML entities (< and >), rendering them harmless.
The danger arises when developers explicitly disable this protection, often using filters like `|safe` in Jinja2 or `|safe` in Django templates. Only mark content as “safe” if you are absolutely certain it contains no user-generated content or if it has been rigorously sanitized first using a library like bleach.
Insecure Deserialization
Serialization is the process of converting an object into a format (like a byte stream) that can be stored or transmitted. Deserialization is the reverse process. Insecure deserialization occurs when an application deserializes untrusted data, which can lead to remote code execution. Python’s `pickle` module is a notorious vector for this because a pickled object can be crafted to execute arbitrary code upon deserialization.
Rule of thumb: Never unpickle data from an untrusted or unauthenticated source. For data interchange between services or with a client, always prefer safer, data-only formats like JSON.
Beyond the Code: Securing Your Environment and Dependencies
Application security extends beyond your own source code. The environment where your code runs and the third-party libraries it depends on are equally critical components of your security posture.

Dependency Management and Vulnerability Scanning
The modern Python application is built on the shoulders of open-source giants. While this accelerates development, it also means you inherit any vulnerabilities present in your dependencies (and their dependencies). The constant stream of python news about newly discovered vulnerabilities in popular packages highlights this risk.
Best Practices:
- Use Virtual Environments: Always use a tool like `venv` or `conda` to isolate project dependencies, preventing conflicts and ensuring a reproducible environment.
- Pin Your Dependencies: Use a `requirements.txt` or `pyproject.toml` file and pin your direct dependencies to specific versions (e.g., `requests==2.28.1`). This prevents unexpected updates from breaking your application or introducing new vulnerabilities. Use tools like `pip-tools` to compile a fully pinned list of all transitive dependencies.
- Regularly Scan for Vulnerabilities: Integrate automated security scanning into your CI/CD pipeline. Tools like pip-audit (now integrated with pip), Safety, and services like GitHub’s Dependabot or Snyk can automatically scan your dependencies against a database of known vulnerabilities and alert you to risks.
Secrets Management: Never Hardcode Credentials
One of the most common and damaging security mistakes is hardcoding sensitive information like API keys, database passwords, and encryption keys directly in source code. Once committed to a version control system like Git, these secrets can be considered compromised, even in private repositories.
Secure Solutions:
- Environment Variables: The most common approach is to store secrets in environment variables. Your application can then read them at runtime. This keeps secrets separate from the codebase.
- Dotenv Files: For local development, `.env` files (used with the `python-dotenv` library) provide a convenient way to manage environment variables. Remember to add `.env` to your `.gitignore` file!
- Secrets Management Services: For production environments, use a dedicated secrets management service like HashiCorp Vault, AWS Secrets Manager, or Google Cloud Secret Manager. These services provide centralized, secure storage with fine-grained access control and audit logging.
import os
from dotenv import load_dotenv
# For local development, loads variables from a .env file
load_dotenv()
# Securely access the API key from the environment
api_key = os.environ.get("API_KEY")
if not api_key:
raise ValueError("API_KEY environment variable not set!")
Proactive Security: Tools, Authentication, and Encryption
A mature security strategy is proactive, not reactive. This involves implementing robust controls for authentication and encryption and using tools to continuously monitor and improve your security posture.
Authentication and Authorization
Authentication (verifying who a user is) and authorization (determining what they are allowed to do) are cornerstones of application security.
- Password Hashing: Never, ever store passwords in plaintext. Use a strong, slow, and salted hashing algorithm. MD5 and SHA1 are broken and should not be used. Modern standards recommend algorithms like Argon2 (the winner of the Password Hashing Competition), scrypt, or bcrypt. Libraries like `argon2-cffi` and `bcrypt` make these easy to use in Python.
- Frameworks: Leverage the built-in authentication and authorization systems provided by mature web frameworks like Django, which handle password hashing, session management, and permissions securely out of the box.
Example of hashing a password with bcrypt:
import bcrypt
password = b"super_secret_password"
# Generate a salt and hash the password
hashed = bcrypt.hashpw(password, bcrypt.gensalt())
# Check a password attempt
is_correct = bcrypt.checkpw(password, hashed) # Returns True
Data Encryption
Encrypting data protects it from being read if it is intercepted or stolen.
- Encryption in Transit: Always use HTTPS (TLS/SSL) for all communication between clients and your server. This prevents man-in-the-middle attacks where an attacker could eavesdrop on or modify traffic.
- Encryption at Rest: Sensitive data stored in your database, on disk, or in backups should be encrypted. While this is often handled at the database or filesystem level, for highly sensitive fields, you may consider application-level encryption using a robust library like cryptography. Be aware that key management is a complex challenge; use high-level APIs from the library unless you have deep expertise in cryptography.
Logging and Monitoring
Comprehensive logging is your best tool for detecting an ongoing attack and for post-incident forensic analysis. Your logs should be a detailed record of important events in your application.
- What to Log: Log all authentication attempts (both successful and failed), password reset requests, changes to permissions, and access to critical or sensitive data.
- What NOT to Log: Never log sensitive data like passwords, session tokens, API keys, or personally identifiable information (PII) in plaintext.
- Use Python’s `logging` Module: Python’s built-in `logging` module is powerful and configurable. Use it to structure your logs and send them to a file or a centralized logging service where they can be monitored and analyzed for anomalies.
Conclusion
Python security is a continuous journey, not a destination. The threat landscape is constantly evolving, and a secure application is one that is built on a solid foundation of defensive principles, maintained with vigilance, and adapted to meet new challenges. By embedding security into your development culture, you can build applications that are not only powerful and functional but also resilient and trustworthy.
The key takeaways are clear: adopt a mindset of zero trust, validate all inputs rigorously, keep your dependencies patched and scanned, manage your secrets with extreme care, and implement strong authentication and encryption. By making these practices a non-negotiable part of your workflow, you contribute to a safer software ecosystem and protect your users, your data, and your reputation.