Python Security Best Practices – Part 4
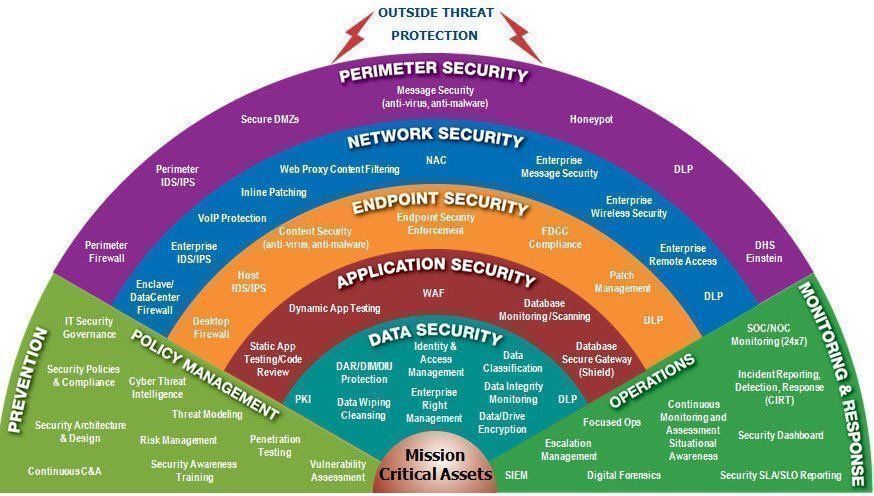
Welcome back to our comprehensive series on Python security. In the previous installments, we laid the groundwork by exploring fundamental security principles. Now, in Part 4, we elevate the discussion to cover advanced techniques and practical implementations essential for building resilient, production-grade Python applications. As threats evolve, so must our defenses. Simply knowing the basics of input validation or password storage is no longer sufficient. Modern applications demand a more sophisticated, layered security posture that anticipates and mitigates complex attack vectors.
This article dives deep into four critical areas: advanced input validation using schema enforcement, mastering modern authentication and authorization, robust secrets management, and securing your software supply chain. We will move beyond theoretical concepts and provide concrete code examples, best practices, and tool recommendations that you can implement immediately. Whether you’re building a web API, a data processing pipeline, or a complex microservices architecture, these principles are universally applicable. Securing your Python applications is not a final destination but a continuous journey of vigilance and improvement. Let’s explore the advanced practices that separate a vulnerable application from a truly secure one.
Advanced Input Validation: Beyond Basic Checks
In our earlier discussions, we touched upon the importance of validating all external input. However, a simple if/else block to check for a data type is merely scratching the surface. Modern applications, especially APIs, receive complex, nested data structures. Manually validating every field is tedious, error-prone, and difficult to maintain. This is where schema validation libraries become indispensable, providing a declarative and robust way to enforce data integrity at the application’s edge.
Embracing Schema Validation with Pydantic
Libraries like Pydantic and Marshmallow transform input validation from an imperative chore into a declarative definition. By defining a data model, you get parsing, validation, and clear error messaging for free. Pydantic, in particular, leverages Python’s type hints to create self-documenting and highly readable models.
Consider a user registration endpoint that accepts a JSON payload. Instead of manually checking each key, you can define a Pydantic model:
from pydantic import BaseModel, EmailStr, Field
from datetime import date
from typing import Optional
class UserRegistration(BaseModel):
username: str = Field(..., min_length=3, max_length=50, pattern=r'^[a-zA-Z0-9_]+$')
email: EmailStr # Built-in validation for email formats
password: str = Field(..., min_length=12)
birth_date: Optional[date] = None
class Config:
anystr_strip_whitespace = True
# Example usage in a web framework like FastAPI
# @app.post("/register")
# async def register_user(user_data: UserRegistration):
# # If the code reaches here, the data is guaranteed to be valid.
# # Pydantic has already parsed, validated, and coerced types.
# # ... proceed with user creation logic ...
# return {"message": f"User {user_data.username} registered successfully."}
In this example, Pydantic automatically handles:
- Type Enforcement: Ensures
usernameandpasswordare strings. - Constraint Checking: Enforces minimum/maximum lengths and regex patterns.
- Specialized Type Validation: The
EmailStrtype validates the email format. - Data Sanitization: The
anystr_strip_whitespaceconfig automatically removes leading/trailing whitespace. - Clear Error Handling: If validation fails, Pydantic raises a detailed
ValidationErrorthat can be easily converted into a user-friendly JSON response, specifying exactly which fields are incorrect and why.
The process, p, you, y, try, t, here, h, often, o, needs, n, this level of rigor to be secure.
Preventing Sophisticated Injection Attacks
While SQL injection is well-known, other forms of injection pose significant threats. The core principle of prevention remains the same: never trust user input and never construct queries or commands by concatenating strings.

- Command Injection: This occurs when an application passes unsafe user-supplied data to a system shell. The most common mistake is using
os.system()or passingshell=Trueto thesubprocessmodule with unvalidated input.Bad:
subprocess.run(f"ping -c 1 {user_input}", shell=True)Good:
subprocess.run(["ping", "-c", "1", user_input], shell=False)By passing arguments as a list (
shell=Falseis the default and safest option), the module ensures that the input is treated as a single argument to the command, not as part of the command itself to be interpreted by the shell. - NoSQL Injection: Applications using MongoDB, Redis, or other NoSQL databases are not immune to injection. If you construct database queries directly from user input, an attacker can manipulate the query structure. For example, in MongoDB, an attacker might inject operators like
$ne(not equal) or$gt(greater than) to bypass authentication checks. Always use the database driver’s provided methods for building queries, which safely handle data types and prevent operator injection.
Mastering Authentication and Authorization
Authentication confirms a user’s identity, while authorization determines what an authenticated user is allowed to do. Getting these right is fundamental to application security, and modern best practices have evolved significantly beyond storing a simple hashed password.
Secure Password Hashing with Modern Algorithms
Storing passwords securely is non-negotiable. Using fast hashing algorithms like MD5 or SHA-256 for passwords is a critical mistake. These algorithms are designed for speed, which makes them vulnerable to brute-force and rainbow table attacks. A modern password hashing function must be:
- Slow and Adaptive: It should be computationally expensive, and its difficulty (work factor) should be tunable to keep pace with increasing hardware speeds.
- Salted: A unique, randomly generated salt must be combined with each password before hashing. This ensures that two identical passwords result in different hashes, rendering pre-computed rainbow tables useless.
The current industry recommendations are Argon2 (the winner of the Password Hashing Competition) and bcrypt. The argon2-cffi library in Python provides a robust implementation.
from argon2 import PasswordHasher
from argon2.exceptions import VerifyMismatchError
ph = PasswordHasher()
# Hashing a new password (e.g., during user registration)
# The hash includes the algorithm, parameters, salt, and the hash itself.
# It is safe to store this entire string in your database.
password = "my_s3cur3_p@ssw0rd!"
hash_string = ph.hash(password)
# Example hash_string: '$argon2id$v=19$m=65536,t=3,p=4$c29tZXNhbHQ$qL/VI8q4aL2D...
# Verifying a password (e.g., during login)
user_provided_password = "my_s3cur3_p@ssw0rd!"
try:
ph.verify(hash_string, user_provided_password)
print("Password is valid.")
except VerifyMismatchError:
print("Invalid password.")
# You can also check if the hash needs to be updated with new parameters
if ph.check_needs_rehash(hash_string):
new_hash = ph.hash(user_provided_password)
# Update the user's hash in the database with new_hash
print("Password hash has been updated to new parameters.")
Implementing Granular Authorization
Once a user is authenticated, you need a robust system to manage their permissions. Hardcoding roles in your business logic (e.g., if user.role == 'admin': ...) quickly becomes unmanageable. A better approach is to implement a structured authorization pattern like Role-Based Access Control (RBAC).
In an RBAC system:
- Permissions are defined for specific actions (e.g., `create_post`, `delete_user`).
- Roles are created as collections of permissions (e.g., an “Editor” role has `create_post` and `edit_own_post` permissions).
- Users are assigned one or more roles.
This decouples permissions from users, making the system far easier to manage and audit. You can implement this using custom decorators in your web framework or leverage libraries like Flask-Principal which provide a sophisticated context-based permission system.
Secrets Management: Protecting Your Crown Jewels
Application secrets include API keys, database credentials, encryption keys, and other sensitive data. One of the most common and dangerous security flaws is hardcoding these secrets directly in source code or configuration files that are committed to version control.
The Dangers of Hardcoded Secrets
When secrets are in your Git repository, they are exposed to anyone with access to the codebase. Even if the repository is private, developer laptops can be compromised, or access can be granted accidentally. Once a secret is committed, it remains in the Git history forever, even if you remove it in a later commit. This makes repository scanning for secrets a primary goal for attackers.
Best Practices for Managing Secrets
The guiding principle is to decouple secrets from code. The application should load them from a secure external source at runtime.
- Environment Variables: This is the most common and fundamental method. Store secrets in the environment where the application runs. For local development, use a
.envfile (which should be added to.gitignore) and load it using a library likepython-dotenv. In production, these variables are set by your deployment platform (e.g., Heroku, AWS Elastic Beanstalk, Kubernetes).# main.py import os from dotenv import load_dotenv # Load variables from .env file for local development load_dotenv() # Safely access the secret api_key = os.getenv("STRIPE_API_KEY") db_password = os.getenv("DATABASE_PASSWORD") if not api_key: raise ValueError("STRIPE_API_KEY environment variable not set.") - Dedicated Secrets Management Tools: For more complex applications or organizations, a dedicated secrets manager is the superior solution. Tools like HashiCorp Vault, AWS Secrets Manager, or Google Cloud Secret Manager provide centralized storage, fine-grained access control, auditing, and automatic secret rotation. Your application is granted a temporary, scoped identity (e.g., an IAM role) that allows it to fetch the secrets it needs at startup. This is the gold standard for modern cloud-native applications.
Securing the Software Supply Chain
Your application is not just the code you write; it’s also the vast ecosystem of open-source libraries you depend on. A vulnerability in one of your dependencies is a vulnerability in your application. Securing this software supply chain is a critical aspect of modern Python development, and staying informed with the latest “python news” and security advisories is essential.
Understanding Dependency Risks
The Python Package Index (PyPI) is an incredible resource, but it’s also a potential attack vector. Threats include:
- Vulnerable Packages: Legitimate packages may have known vulnerabilities (CVEs) that have not been patched in the version you are using.
- Malicious Packages (Typosquatting): Attackers publish packages with names similar to popular ones (e.g.,
python-requestsinstead ofrequests), hoping developers will make a typo during installation. These packages can contain malware that executes upon installation. - Dependency Confusion: An attacker can publish a package with the same name as an internal, private package to a public repository. If the build system is not configured correctly, it might pull the malicious public version instead of the internal one.
Tools and Best Practices for Dependency Security
Proactive management is key to mitigating these risks.
- Pin Your Dependencies: Always use a dependency management tool like Poetry or pip-tools to generate a lock file (
poetry.lockorrequirements.txtwith pinned versions likerequests==2.28.1). This ensures that you are always installing the exact same version of every dependency, creating reproducible and predictable builds. - Regularly Scan for Vulnerabilities: Integrate automated security scanning into your CI/CD pipeline. Tools like
pip-audit(from the Python Packaging Authority),safety, or services like Snyk and GitHub’s Dependabot can scan your lock file against a database of known vulnerabilities and alert you to insecure dependencies.# Example of running pip-audit python -m pip install pip-audit pip-audit -r requirements.txt - Use a Private Package Repository: For organizations with internal libraries, use a private repository like Artifactory or PyPI Cloud. This prevents dependency confusion attacks and gives you a centralized point to vet and cache approved open-source packages.
Conclusion
In this fourth part of our series, we have moved from foundational concepts to the advanced, practical techniques required to secure modern Python applications. We’ve seen how declarative schema validation with Pydantic provides a superior defense against bad data. We’ve reinforced the necessity of using slow, salted, and adaptive algorithms like Argon2 for password hashing and the importance of structured authorization. We’ve established the non-negotiable rule of externalizing secrets from your codebase, using environment variables or dedicated secret managers. Finally, we’ve highlighted the critical importance of securing your software supply chain by pinning, scanning, and vetting your dependencies.
Security is a multifaceted discipline that requires continuous learning and diligence. By integrating these advanced practices into your development lifecycle, you build multiple layers of defense, creating applications that are not only functional and efficient but also resilient against the sophisticated threats of today’s digital landscape.