Django REST Framework Best Practices – Part 2
Welcome back to our comprehensive series on mastering Django REST Framework. In Part 1, we laid the groundwork, covering the essentials of building robust APIs. Now, it’s time to elevate your skills. This guide delves into the advanced best practices that separate good APIs from great ones. We will explore sophisticated techniques for serialization, implement granular security with custom authentication and permissions, and tackle the critical aspects of performance, versioning, and testing. By mastering these concepts, you’ll be equipped to build REST APIs that are not just functional but also scalable, secure, and exceptionally maintainable, keeping you ahead in the fast-paced world of Python web development.
Building a simple CRUD API is one thing; engineering an application that can handle complex data relationships, withstand security threats, and scale gracefully under load is another. This article provides practical, actionable insights and code examples to help you navigate these advanced challenges, ensuring your projects adhere to the highest professional standards.
Mastering Advanced Serialization Techniques
Serializers are the heart of DRF, translating complex data types, like Django querysets and model instances, into native Python datatypes that can then be easily rendered into JSON, XML, or other content types. While basic model serialization is straightforward, real-world applications often demand more nuance and performance optimization.
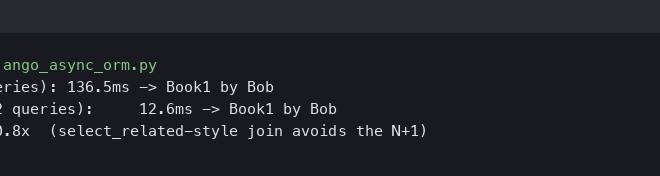
Tackling the N+1 Query Problem
One of the most common performance bottlenecks in DRF applications is the “N+1 query” problem. This occurs when you serialize a list of objects, and for each object, the serializer makes an additional database query to fetch a related object. For example, if you have 100 blog posts and each has an author, a naive serializer might execute 1 query for the posts and 100 additional queries for the authors, totaling 101 queries.
The solution is to be proactive in fetching related data. Django’s ORM provides two powerful tools for this: select_related and prefetch_related.
select_related: Works by creating an SQL join and including the fields of the related object in theSELECTstatement. It’s best for foreign key and one-to-one relationships.prefetch_related: Works by doing a separate lookup for each relationship and doing the “joining” in Python. It’s ideal for many-to-many and many-to-one relationships.
You should apply these optimizations at the earliest possible point—typically in the get_queryset method of your ViewSet.
Example: Optimizing a ViewSet
Consider a model for an Article with a foreign key to the Author model.
# In views.py
from rest_framework import viewsets
from .models import Article
from .serializers import ArticleSerializer
# Inefficient ViewSet (causes N+1 problem)
class InefficientArticleViewSet(viewsets.ReadOnlyModelViewSet):
queryset = Article.objects.all()
serializer_class = ArticleSerializer
# Optimized ViewSet
class ArticleViewSet(viewsets.ReadOnlyModelViewSet):
serializer_class = ArticleSerializer
def get_queryset(self):
"""
Optimize the queryset to prevent N+1 queries by pre-fetching
related Author and Tags data.
"""
return Article.objects.select_related('author').prefetch_related('tags').all()
By overriding get_queryset, we ensure that for any list request, only three database queries will be made: one for the articles, one for the authors, and one for the tags, regardless of how many articles are returned.
Handling Complex Relationships with Nested Serializers and Custom Fields
Representing related data is a core task. While nested serializers are a great default, they can sometimes lead to bulky responses or unwanted data exposure. DRF provides several ways to customize this behavior.
Using `SerializerMethodField` for Computed Data
Sometimes, a field in your API response isn’t a direct mapping of a model field but a computed value. SerializerMethodField is perfect for this. For instance, you might want to show a user’s full name or calculate the number of comments on an article.
# In serializers.py
from rest_framework import serializers
from .models import Article
class ArticleSerializer(serializers.ModelSerializer):
author_full_name = serializers.SerializerMethodField()
comment_count = serializers.SerializerMethodField()
class Meta:
model = Article
fields = ['id', 'title', 'content', 'author_full_name', 'comment_count']
def get_author_full_name(self, obj):
# obj is the Article instance
return f"{obj.author.first_name} {obj.author.last_name}"
def get_comment_count(self, obj):
# Assumes a 'comments' related_name on the Article model
return obj.comments.count()
Fortifying Your API with Custom Authentication and Permissions
Security is not an optional feature. While DRF provides excellent defaults like IsAuthenticated, real-world applications often require more granular control. This means implementing custom logic to determine who can access what and under which conditions.
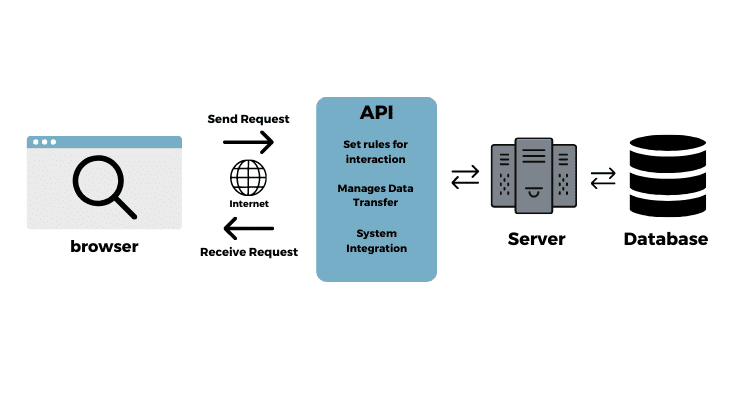
Implementing JWT for Stateless Authentication
While session-based and basic token authentication work well, JSON Web Tokens (JWT) have become a standard for modern, stateless APIs, especially those consumed by single-page applications (SPAs) or mobile apps. The server doesn’t need to store token information, making the system more scalable.
The djangorestframework-simplejwt package is a popular and well-maintained choice. After installation, you configure it in your settings.py.
# In settings.py
REST_FRAMEWORK = {
'DEFAULT_AUTHENTICATION_CLASSES': (
'rest_framework_simplejwt.authentication.JWTAuthentication',
),
# ... other settings
}
This package provides endpoints for obtaining, refreshing, and verifying tokens, creating a secure and stateless authentication flow.
Granular Control with Object-Level Permissions
Global permissions like IsAuthenticated or IsAdminUser check for access at the view level. But what if you need to check if a user is allowed to edit a *specific* object? For example, a user should only be able to edit their own profile, not someone else’s. This is where object-level permissions come in.
To implement this, you create a custom permission class that inherits from BasePermission and implements the has_object_permission method.
Example: Custom Permission for Object Ownership
# In permissions.py
from rest_framework import permissions
class IsOwnerOrReadOnly(permissions.BasePermission):
"""
Custom permission to only allow owners of an object to edit it.
Assumes the model instance has an `owner` attribute.
"""
def has_object_permission(self, request, view, obj):
# Read permissions are allowed to any request,
# so we'll always allow GET, HEAD or OPTIONS requests.
if request.method in permissions.SAFE_METHODS:
return True
# Write permissions are only allowed to the owner of the snippet.
# This assumes your model has a field named 'owner' or 'user'.
return obj.owner == request.user
You can then apply this permission to your ViewSet:
# In views.py
from rest_framework import viewsets
from .models import UserProfile
from .serializers import UserProfileSerializer
from .permissions import IsOwnerOrReadOnly
from rest_framework.permissions import IsAuthenticated
class UserProfileViewSet(viewsets.ModelViewSet):
queryset = UserProfile.objects.all()
serializer_class = UserProfileSerializer
# Apply both permissions. The user must be authenticated first,
# then the object-level permission is checked for unsafe methods.
permission_classes = [IsAuthenticated, IsOwnerOrReadOnly]
Scaling Your API: Versioning, Throttling, and Documentation
As your API grows and gains users, managing its evolution and protecting it from abuse become paramount. These practices ensure your API remains stable, predictable, and performant for all consumers.
Implementing a Clear API Versioning Strategy
Breaking changes are inevitable. API versioning allows you to introduce these changes without disrupting existing client applications. DRF supports several versioning schemes, with URLPathVersioning being one of the most explicit and popular.
You configure it in settings.py and then structure your urls.py accordingly.
# In settings.py
REST_FRAMEWORK = {
'DEFAULT_VERSIONING_CLASS': 'rest_framework.versioning.URLPathVersioning',
# ...
}
# In urls.py
from django.urls import path, include
from myapp.views import ArticleViewSet
# Example for v1
router_v1 = routers.DefaultRouter()
router_v1.register(r'articles', ArticleViewSet, basename='article-v1')
# Main URL configuration
urlpatterns = [
path('api/v1/', include(router_v1.urls)),
# path('api/v2/', include(router_v2.urls)), # Future version
]
This makes it clear to consumers which version of the API they are targeting (e.g., /api/v1/articles/).
Preventing Abuse with Throttling
Throttling, or rate limiting, is essential for protecting your API from denial-of-service attacks or runaway scripts from a single user. DRF’s throttling is highly configurable.
You can set global policies and then create more specific “scopes” for sensitive endpoints.
# In settings.py
REST_FRAMEWORK = {
'DEFAULT_THROTTLE_CLASSES': [
'rest_framework.throttling.AnonRateThrottle',
'rest_framework.throttling.UserRateThrottle'
],
'DEFAULT_THROTTLE_RATES': {
'anon': '100/day',
'user': '1000/hour',
'signup': '5/minute' # Custom scope
}
}
To apply a custom scope, you set the throttle_scope property on a view.
# In views.py
from rest_framework.views import APIView
from rest_framework.response import Response
class UserSignUpView(APIView):
throttle_scope = 'signup'
def post(self, request, format=None):
# ... signup logic ...
return Response({'status': 'user created'})
This ensures the critical sign-up endpoint can’t be spammed, while general API usage for authenticated users remains generous.
Ensuring Reliability with a Robust Testing Strategy
An untested API is a broken API waiting to happen. In the world of professional Python development, testing is a non-negotiable part of the development lifecycle. DRF provides excellent tools, chief among them the APIClient and APITestCase, to make API testing effective and straightforward.
Your tests should cover:
- Success Cases: Does the endpoint return the correct data and status code (e.g., 200 OK, 201 Created) for valid requests?
- Failure Cases: Does it handle bad data gracefully with a 400 Bad Request?
- Authentication: Does it correctly return a 401 Unauthorized or 403 Forbidden for users without the right credentials or permissions?
- Business Logic: Does the endpoint correctly perform the action it’s supposed to?
Example: Writing a Test Case for an Endpoint
Here is a test for an endpoint that lists articles, ensuring it’s protected and returns the correct data.
# In tests.py
from django.contrib.auth.models import User
from rest_framework import status
from rest_framework.test import APITestCase
from .models import Article, Author
class ArticleAPITests(APITestCase):
def setUp(self):
# Create a user for authentication
self.user = User.objects.create_user(username='testuser', password='password123')
# Create some data
self.author = Author.objects.create(user=self.user, bio="Test bio")
self.article = Article.objects.create(
title="Test Article",
content="Some content here.",
author=self.author
)
def test_list_articles_unauthenticated(self):
"""
Ensure unauthenticated users cannot access the article list.
"""
response = self.client.get('/api/v1/articles/')
self.assertEqual(response.status_code, status.HTTP_401_UNAUTHORIZED)
def test_list_articles_authenticated(self):
"""
Ensure authenticated users can access the article list and see the data.
"""
# Force authenticate the client with our user
self.client.force_authenticate(user=self.user)
response = self.client.get('/api/v1/articles/')
# Check for success status code
self.assertEqual(response.status_code, status.HTTP_200_OK)
# Check that the response contains one article
self.assertEqual(len(response.data), 1)
# Check the content of the returned article
self.assertEqual(response.data[0]['title'], 'Test Article')
This test case validates both the security and the functionality of the endpoint, providing confidence that your API behaves as expected. Staying current with development news and patterns in the testing community can further refine your approach.
Conclusion
Moving beyond the basics of Django REST Framework is where you truly begin to build professional, resilient, and scalable APIs. In this guide, we’ve explored the critical best practices that define high-quality API development. By optimizing your serializers to prevent performance traps, implementing granular custom permissions for robust security, managing your API’s lifecycle with versioning, protecting it with throttling, and guaranteeing its reliability through comprehensive testing, you are building a foundation for success. These advanced techniques are not just features; they are essential practices for any serious backend developer working with Python and Django. Continue to apply these principles, and you will consistently deliver APIs that are a pleasure for developers to consume and that can stand the test of time and scale.