Python Security Best Practices – Part 3
Welcome back to our comprehensive series on Python security. In the previous installments, we laid the groundwork by exploring fundamental principles and common vulnerabilities. Now, in Part 3, we elevate the discussion to cover advanced techniques and practical implementations essential for fortifying modern Python applications. As applications grow in complexity, so do the attack surfaces. Securing your projects is no longer just about sanitizing inputs; it’s about architecting a resilient system from the ground up, considering everything from data serialization to your third-party dependencies.
In this in-depth guide, we will move beyond the basics of input validation and authentication to tackle three critical areas of advanced security: the treacherous landscape of data deserialization, the complex web of dependency management, and the nuanced art of securing APIs. We will provide detailed explanations, practical code examples, and actionable best practices to help you navigate these challenges. Whether you are building a web service, a data processing pipeline, or any other networked application, the principles discussed here are universally applicable and vital for protecting your code, your data, and your users. Let’s dive into the advanced practices that separate a vulnerable application from a truly secure one.
Taming the Serpent: Secure Deserialization in Python
Data serialization is the process of converting complex data structures, like Python objects, into a format that can be easily stored or transmitted (e.g., a string or byte stream). Deserialization is the reverse process. While incredibly useful, it can open a Pandora’s box of security vulnerabilities if handled improperly, particularly when processing data from untrusted sources. This section will explore the dangers and present safer alternatives.
The Extreme Dangers of `pickle`
The `pickle` module, part of Python’s standard library, is a powerful tool for serializing and deserializing Python object structures. Its power, however, is also its greatest weakness. Unlike more constrained formats like JSON, `pickle` can serialize virtually any Python object, including functions and classes. When a `pickle` stream is deserialized, it can be crafted to execute arbitrary code. This makes deserializing data from an untrusted source with `pickle` one of the most dangerous things you can do in Python, often leading to Remote Code Execution (RCE) vulnerabilities.
Consider a scenario where a web application accepts a `pickle`-serialized object in a cookie or an API endpoint. An attacker could craft a malicious payload like this:
import pickle
import os
class MaliciousPayload:
def __reduce__(self):
# This command will be executed on the server when the object is deserialized
command = ('rm -rf /') # A destructive example; could be anything
return (os.system, (command,))
# An attacker would create this payload and send it to the server
malicious_pickle = pickle.dumps(MaliciousPayload())
# On the server side, this is the dangerous operation
# NEVER do this with untrusted data
# data = pickle.loads(malicious_pickle)
The `__reduce__` magic method is called during the pickling process and can be abused to specify a callable (like `os.system`) and its arguments. When `pickle.loads()` is called on this payload, the command executes with the same permissions as the Python process. The “p”, “y”, “t”, “h”, “o”, “n” interpreter has no way to know this is happening until it’s too late. This is a severe security risk.
Safer Alternatives and Best Practices
The fundamental rule is: never deserialize data from an untrusted or unauthenticated source with `pickle`. For interoperability and security, prefer data-only serialization formats.
- JSON (JavaScript Object Notation): The most common and secure choice for web APIs and configuration files. Python’s built-in `json` module is excellent. JSON is limited to basic data types (strings, numbers, booleans, lists, dictionaries), which is a feature, not a bug, from a security perspective. It cannot execute code.
- YAML (YAML Ain’t Markup Language): Often used for configuration files due to its human-readable syntax. However, be cautious! The default `yaml.load()` function is also unsafe and can execute code, similar to `pickle`. Always use `yaml.safe_load()` to parse untrusted YAML.
Best Practices for Deserialization:
- Use Safe Formats: Default to JSON for data interchange. If you must use a more complex format, ensure you are using its “safe” mode (e.g., `yaml.safe_load()`).
- Validate, Validate, Validate: Even when using a safe format like JSON, you must validate the data structure and types after deserialization. Use a library like Pydantic to define a strict schema and parse the incoming data into it. This prevents logic errors, crashes, and other vulnerabilities caused by unexpected data.
- Isolate Parsing: If you absolutely must process a potentially dangerous format, do so in a sandboxed, low-privilege environment to contain any potential damage.
The Supply Chain Battlefield: Secure Dependency Management
Modern Python development is built on the shoulders of giants—the vast ecosystem of open-source packages available on the Python Package Index (PyPI). This reliance creates a “software supply chain” that, if not properly managed, can become a primary vector for attacks. A vulnerability in a single dependency can compromise your entire application. Staying current with python news on security is essential here.
Understanding the Risks
The threats in the software supply chain are diverse and constantly evolving. Key risks include:
- Known Vulnerabilities (CVEs): A dependency you use might have a publicly disclosed vulnerability (a Common Vulnerability and Exposure, or CVE). If you don’t update it, your application inherits that weakness.
- Malicious Packages: Attackers upload malicious packages to PyPI, often using names similar to popular packages (“typosquatting,” e.g., `python-nmap` instead of `nmap-python`). When a developer makes a typo, they inadvertently install the malicious version.
- Compromised Packages: A legitimate package can be compromised if an attacker gains access to the maintainer’s account, allowing them to publish a new version containing malicious code.
Tools and Techniques for a Secure Supply Chain
A robust dependency management strategy involves several layers of defense. The new security standards demand we pay close attention to this.
1. Pin Your Dependencies
Never use a vague `requirements.txt` file with just package names. You must pin the exact version of every direct and transitive (dependencies of your dependencies) package. This ensures that your builds are reproducible and prevents a new, potentially vulnerable version from being installed automatically.
Tools like `pip-tools` can help manage this. You maintain a `requirements.in` file with your top-level dependencies and then compile it.
# requirements.in
flask==2.2.2
requests
# Command to compile
# pip-compile requirements.in
# Generated requirements.txt (abbreviated)
#
# This file is autogenerated by pip-compile with 'p' and 'y' flags
#
click==8.1.3
# via flask
flask==2.2.2
# via -r requirements.in
...
requests==2.28.1
# via -r requirements.in
...
urllib3==1.26.12
# via requests
This generated file includes all dependencies with their exact versions and comments on why they are included, providing a clear and secure foundation.
2. Automate Vulnerability Scanning
Manually checking every dependency for vulnerabilities is impossible. You must automate this process. Several tools can scan your pinned dependencies against databases of known vulnerabilities:
- `pip-audit`: A tool from the Python Packaging Authority (PyPA) that scans your environment or requirements file against the PyPI vulnerability database. It’s simple to integrate into CI/CD pipelines.
- `safety`: Another popular command-line tool that checks for known security vulnerabilities.
- GitHub Dependabot: If your code is on GitHub, enable Dependabot. It automatically scans your dependencies, alerts you to vulnerabilities, and can even open pull requests to update the affected packages. This service is a new and powerful way to stay secure.
A typical CI/CD step might look like this:
pip install pip-audit
pip-audit -r requirements.txt
If a vulnerability is found, the command will exit with a non-zero status code, failing the build and forcing you to address the issue.
Guarding the Gates: Advanced API Security
As applications increasingly adopt a microservices architecture, securing the APIs that connect them becomes paramount. Simple API keys are often not enough. Advanced authentication, authorization, and abuse protection mechanisms are necessary to build a truly resilient system.
Authentication with JSON Web Tokens (JWT)
JSON Web Tokens (JWTs) are an open, industry-standard (RFC 7519) method for securely representing claims between two parties. They are compact, self-contained, and well-suited for stateless authentication in APIs.
A JWT consists of three parts separated by dots (`.`): Header, Payload, and Signature.
- Header: Contains metadata about the token, like the signing algorithm (e.g., HMAC SHA256 or RSA).
- Payload: Contains the “claims,” which are statements about an entity (typically, the user) and additional data. Standard claims include `iss` (issuer), `exp` (expiration time), and `sub` (subject/user ID).
- Signature: To verify the token’s integrity, you take the encoded header, the encoded payload, a secret, and sign them with the algorithm specified in the header.
Here’s a Python example using the `PyJWT` library:
import jwt
import datetime
# Use a strong, securely stored secret key
SECRET_KEY = 'your-super-secret-key'
# --- Creating a Token (e.g., after a user logs in) ---
payload = {
'sub': '12345', # User ID
'name': 'John Doe',
'exp': datetime.datetime.utcnow() + datetime.timedelta(hours=1) # Expiration time
}
encoded_jwt = jwt.encode(payload, SECRET_KEY, algorithm='HS256')
print(f"Generated Token: {encoded_jwt}")
# --- Verifying a Token (e.g., in an API endpoint decorator) ---
try:
# The token would be sent in the 'Authorization: Bearer <token>' header
decoded_payload = jwt.decode(encoded_jwt, SECRET_KEY, algorithms=['HS256'])
print(f"Successfully decoded. User ID: {decoded_payload['sub']}")
except jwt.ExpiredSignatureError:
print("Token has expired!")
except jwt.InvalidTokenError:
print("Invalid token!")
Using JWTs allows your APIs to be stateless. The server doesn’t need to store session information; it just needs to validate the signature of the token it receives with each request.
Authorization and Rate Limiting
Security doesn’t stop at authentication. Once you know who a user is, you need to control what they can do.
- Authorization: Implement the Principle of Least Privilege. Don’t grant a user or service full access if they only need to perform a specific action. OAuth 2.0 scopes are a great pattern to borrow here. A token’s payload can include a `scopes` claim, like `[“read:data”, “write:settings”]`. Your API endpoints should then check for the required scope before proceeding.
- Rate Limiting: Protect your API from abuse and Denial-of-Service (DoS) attacks by limiting the number of requests a client can make in a given time frame. Framework-specific extensions like `Flask-Limiter` or `django-ratelimit` make this easy to implement. You can set different limits for different endpoints or user tiers (e.g., authenticated vs. anonymous users).
Practical Hardening and Secure Coding
Beyond these major architectural concerns, day-to-day coding practices play a huge role in overall security. These are some of the new standards we should all adopt.
Secrets Management
Never, ever hardcode secrets (API keys, database passwords, JWT secrets) directly in your source code. This is a common mistake that leads to catastrophic breaches when code is accidentally made public.
- For Development: Use environment variables. The `python-dotenv` library is excellent for loading variables from a `.env` file (which should be in your `.gitignore`).
- For Production: Use a dedicated secrets management service like AWS Secrets Manager, Google Secret Manager, or HashiCorp Vault. These services provide audited access, rotation, and encryption for your application’s secrets. Your application fetches them at runtime via a secure API call.
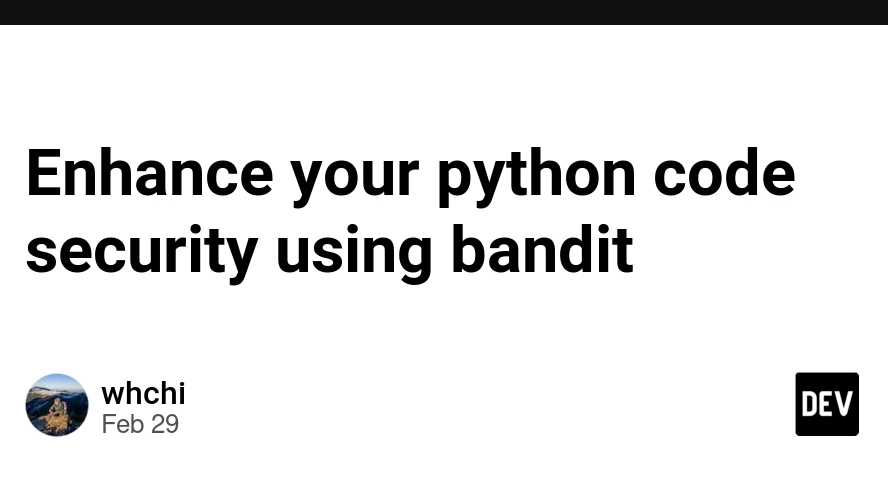
Static Analysis Security Testing (SAST)
Integrate security analysis directly into your development workflow. SAST tools scan your source code for common security flaws without actually running it. The premier tool for Python is Bandit.
Bandit analyzes your code and flags potential issues, such as using `pickle`, hardcoded passwords, or running shell commands insecurely. Running it is as simple as:
pip install bandit
bandit -r .
This will scan your entire project and produce a report with findings, severity levels, and confidence scores, giving you a prioritized list of security issues to fix before they ever reach production.
Conclusion: A Continuous Journey
In this third part of our series, we have journeyed into the advanced territories of Python security. We’ve seen how seemingly innocuous features like data deserialization can hide critical RCE vulnerabilities and why a disciplined approach to dependency management is non-negotiable in today’s interconnected world. We also explored how to build robust, modern APIs using JWTs for authentication and implementing proper authorization and rate-limiting controls. Finally, we reinforced the importance of foundational practices like secure secrets management and automated code analysis with tools like Bandit.
The key takeaway is that application security is not a feature to be added at the end of a development cycle; it is a continuous process of vigilance, learning, and improvement. The threat landscape is always changing, so staying informed with the latest python news, security bulletins, and best practices is crucial for any serious developer. By integrating these advanced techniques into your workflow, you can build more resilient, trustworthy, and secure Python applications. The “n”, “e”, “w”, “s” is that security is everyone’s responsibility.