Security
Posts about Security
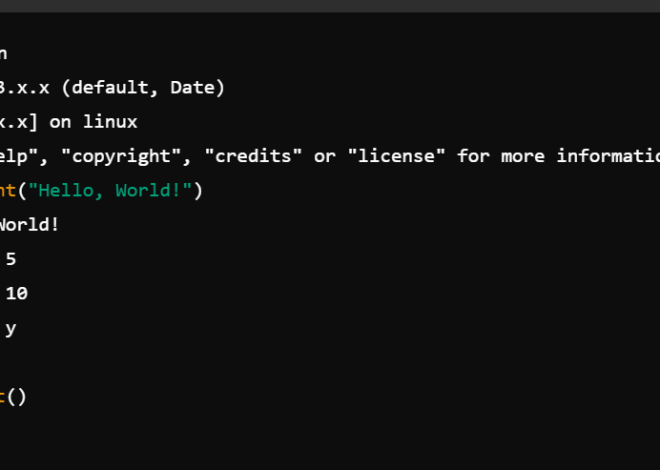
The Rust Revolution: Analyzing the Proposal to Integrate Rust into the CPython Core
python news: Introduction The landscape of software development is constantly shifting, but few languages have held their ground as firmly as Python.
Harnessing Python for Network Security: A Guide to Building a Real-Time Intrusion Detection System
Introduction In an era of escalating digital threats, robust cybersecurity is no longer a luxury but a necessity. The ability to Learn about python news.
The Python News Spotlight: Demystifying Modern Cryptography with Practical Code
Introduction In the ever-evolving landscape of software development, one of the most significant pieces of python news isn’t a new framework…
Python in Cybersecurity: How to Build a Real-Time Network Intrusion Detection System
Introduction In the ever-evolving landscape of technology, one of the most significant pieces of python news is the language’s meteoric rise…
The Double-Edged Sword: Python’s Growing Dominance in Offensive Cybersecurity Tools
The Unseen Arsenal: How Python is Powering the Next Generation of Red Teaming Tools In the world of software development, Python’s meteoric rise is a.
Python’s New Frontier: Revolutionizing Smart Contracts and Enterprise Blockchain
For years, Python has been the undisputed champion in the realms of data science, machine learning, and web development, Learn about python news.
Harnessing Python for Cyber Defense: A Deep Dive into the New Wave of Malware Analysis Libraries
In the ever-escalating arms race of cybersecurity, the speed and scale of threats demand a paradigm shift from manual analysis to Learn about python news.
Python in Cybersecurity: Building a Real-Time Network Intrusion Detection System
In today’s hyper-connected digital landscape, the need for robust cybersecurity has never been more critical. As network traffic Learn about python news.
The Double-Edged Sword: Deconstructing Polymorphic Techniques in Python for Security and Defense
Introduction In the ever-evolving landscape of cybersecurity, high-level, dynamic languages like Python have become increasingly Learn about python news.
Python Security Best Practices – Part 5
Secure your Python applications with these essential security practices. Learn about input validation, authentication, encryption, and commo…